Proteja sua organização da nova geração de ameaças
Para proteger sua organização contra ataques cibernéticos em constante evolução e avanço, você precisa de uma plataforma que ofereça proteção zero trust abrangente contra ameaças cibernéticas na velocidade e escala da nuvem.
Impeça as ameaças antes que elas se tornem ataques
Elimine os produtos específicos e a complexidade
Impeça a movimentação lateral de ameaças
Veja e priorize seus maiores riscos
O problema
As abordagens centradas em VPNs e firewalls não conseguem mais proteger contra ataques cibernéticos
86%
56%
400%
Um ataque cibernético é como um assalto a banco

Os invasores encontram você
IPs detectáveis são vulneráveis, até mesmo firewalls e VPNs, que são destinados a proteger você em primeiro lugar.
Eles comprometem você
Os invasores exploram vulnerabilidades para estabelecer uma base em sua rede.
Eles se movem lateralmente
Assim que uma máquina é infectada, toda a rede fica comprometida.
Eles roubam os seus dados
Os dados confidenciais em aplicativos, servidores e redes inteiras são perdidos.
Visão geral da solução
Defesa contra ameaças holística e preparada para o futuro
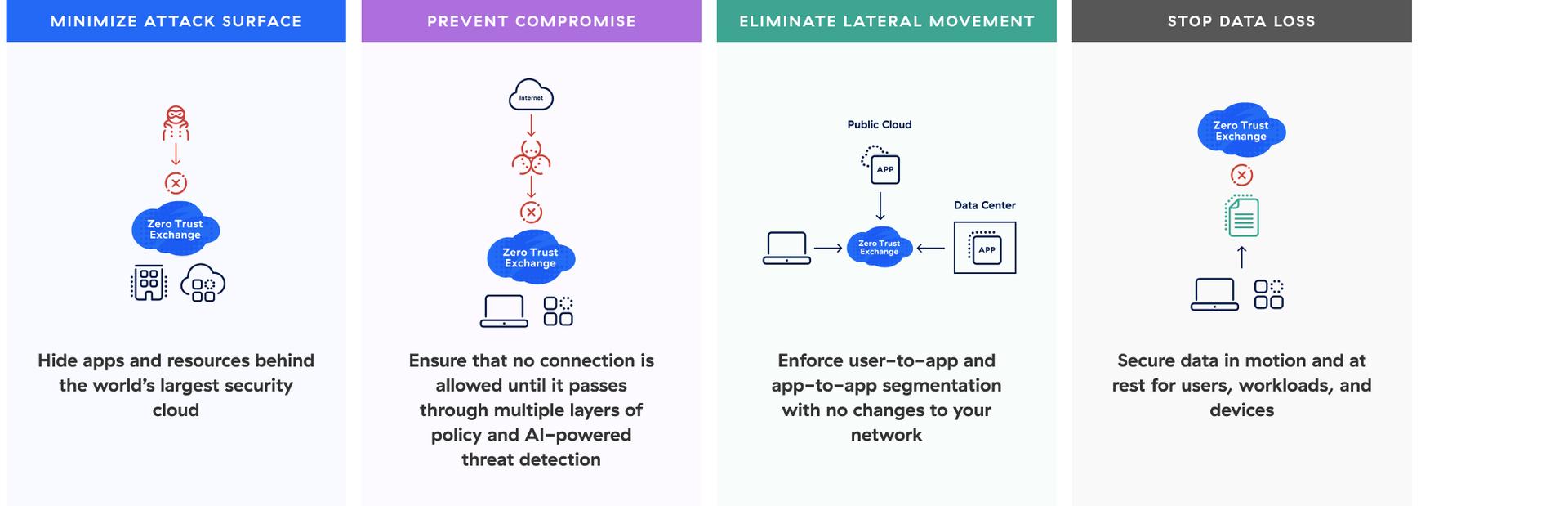
A plataforma nativa da nuvem Zscaler Zero Trust Exchange™ combate cada etapa da cadeia de ataque. Essa abordagem holística corresponde à estrutura MITRE ATT&CK para minimizar a superfície de ataque, evitar comprometimentos, eliminar movimentações laterais e impedir a perda de dados.
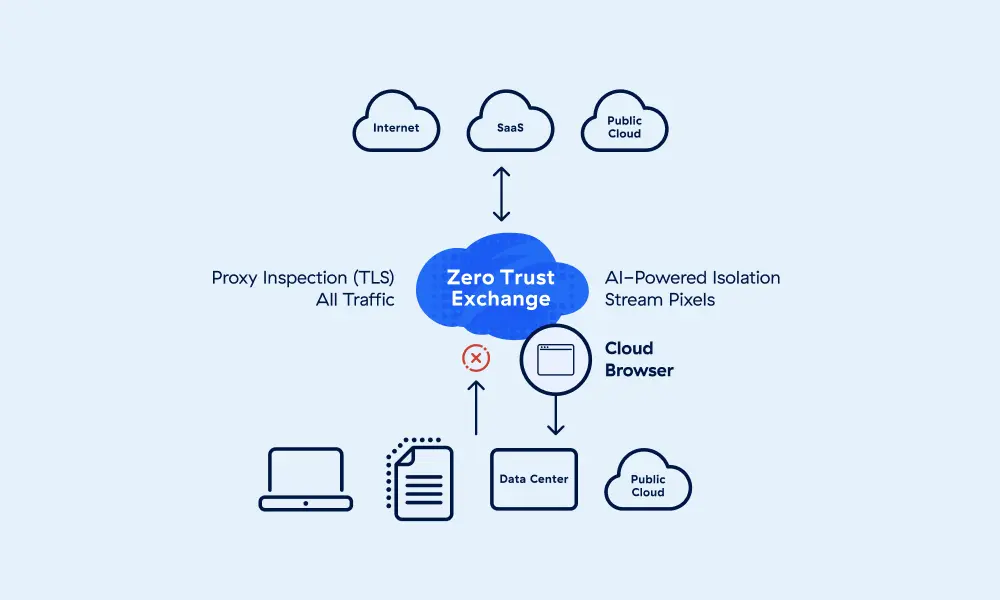
Desenvolvida com base no princípio de privilégio mínimo, nossa arquitetura de proxy oferece inspeção completa de TLS/SSL em larga escala, com conexões intermediadas entre usuários e aplicativos com base na identidade, contexto e políticas empresariais.
Benefícios
O que diferencia a Zscaler Cyberthreat Protection?
Proteja todos os quatro estágios de um ataque cibernético
Minimize a superfície de ataque, previna comprometimentos, elimine a movimentação lateral e evite a perda de dados.
Proteja os usuários contra ameaças cibernéticas em linha
Bloqueie ameaças antes que elas entrem em seus sistemas com a proteção contra ameaças com tecnologia de IA.
Reduza a complexidade com uma arquitetura baseada na nuvem
Desative hardwares legados e produtos para fins específicos, simplificando o gerenciamento e gerando economia.
Entenda os maiores riscos para sua organização
Obtenha insights práticos sobre riscos e fluxos de trabalho guiados para remediação.
Detalhes da solução
Minimizar a superfície de ataque
Criminosos não podem atacar o que não conseguem ver. Ao ocultar seus aplicativos, locais e dispositivos na Internet, a Zscaler evita que os criminosos alcancem e invadam esses ativos.

Principais ofertas
Obtenha uma visão holística do que está exposto à internet, vulnerabilidades e fraquezas em TLS/SSL.
Impeça o acesso não autorizado a sistemas críticos (SSH/RDP/VNC).
Mantenha usuários, filiais e fábricas ocultas por atrás da Zero Trust Exchange.
Evite o comprometimento
Elimine ataques de phishing, downloads de malware e mais com inspeção completa em larga escala de TLS em linha e prevenção de ameaças baseada em IA, informada por mais de 400 bilhões de transações empresariais diárias.
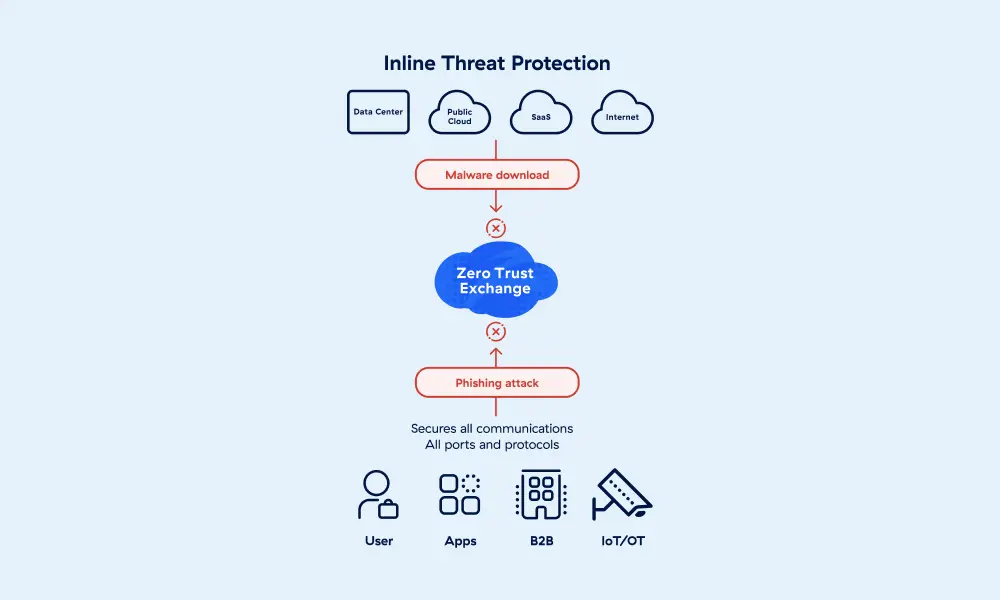
Principais ofertas
Proteja todas as portas e protocolos.
Transforme conteúdo arriscado da web em um fluxo de pixels seguro e dinâmico.
Obtenha proteção baseada em assinatura de mais de 60 feeds de ameaças.
Aproveite varredura de conteúdo, correlação e pontuação de risco.
Eliminar a movimentação lateral
A segmentação zero trust não requer segmentação de rede — sua rede é simplesmente o transporte. Minimize o raio de ação, defenda-se contra ameaças internas e reduza a sobrecarga operacional.
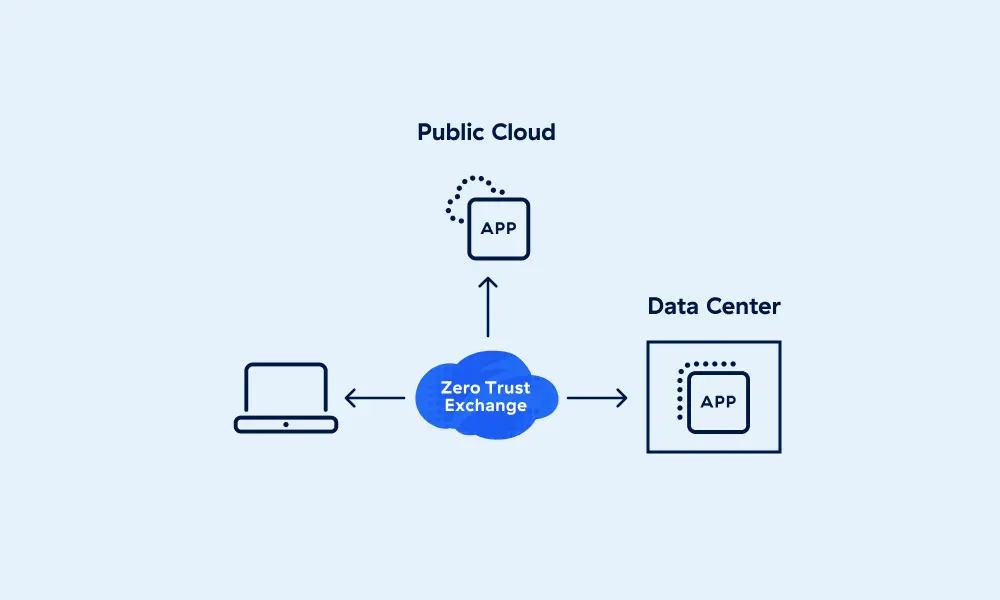
Principais ofertas
Implemente a segmentação de usuário para aplicativo e de aplicativo para aplicativo.
Controle o acesso de usuário a sistemas críticos (SSH/RDP/VNC).
Implante iscas para detectar e impedir que usuários infectados se movam lateralmente.
Mantenha a postura e a higiene da identidade, além da detecção ativa de ameaças.
Aproveite OWASP Top 10, CVE e proteções personalizadas para tráfego de aplicativos.
Impeça a perda de dados
Descubra aplicativos perigosos e da TI invisível com classificação automática de dados confidenciais. Proteja o usuário, a carga de trabalho e o tráfego IoT/TO para dados em repouso e dados em movimento com e-mail integrado, DLP de terminal e inspeção TLS em larga escala.
Principais ofertas
Proteja dados confidenciais na web, e-mail e aplicativos de GenAI.
Proteja portas USB, impressão, compartilhamento de rede, clientes de sincronização, modo off-line.
Aplique controles de aplicativos e compartilhamento e restrições de utilização.
Encerre configurações incorretas de risco em plataformas SaaS como Microsoft 365 e Google Workspace.
Proteja dados na nuvem pública com descoberta de dados aprofundada e gerenciamento de postura.
Ofereça acesso seguro a dados para terminais não gerenciados e dispositivos pessoais.
Impeça a perda de dados para aplicativos de GenAI de risco com visibilidade detalhada dos prompts.
Faça um tour autoguiado
Impeça ataques cibernéticos avançados como ransomware, ataques à cadeia de suprimentos, phishing e muito mais com proteção avançada contra ameaças proprietária.
Alianças em destaque



The Zscaler Platform
The cybersecurity platform for the AI Age - built on Zero Trust to protect users, workloads, branches and devices through the world’s largest inline security cloud.

Data Security
Secure data everywhere, with comprehensive visibility and controls across all channels.
AI Security
Embrace AI with confidence using Zscaler AI Protect, a unified solution to secure AI at scale.
Agentic SecOps
Draw on insights from the world’s largest inline security cloud and third-party sources to assess risk and detect and contain breaches.
Perguntas frequentes
Perguntas frequentes
Proteção contra ameaças cibernéticas é uma categoria de soluções de segurança criadas para ajudar os profissionais de segurança a proteger sistemas e redes contra malware e outros ataques cibernéticos direcionados. Esses ataques tentam se infiltrar em sistemas ou redes para interromper serviços ou roubar dados, geralmente gerando lucro para os invasores. Leia o artigo
Zero trust é uma estratégia de segurança que afirma que nenhuma entidade (usuário, aplicativo, serviço ou dispositivo) deve ser considerada confiável por padrão. Seguindo o princípio do acesso de privilégio mínimo, antes que qualquer conexão seja permitida, a confiança é estabelecida com base no contexto da entidade e na postura de segurança, e então é continuamente reavaliada para cada nova conexão, mesmo que a entidade já tenha sido autenticada antes. Leia o artigo
Os ataques de ransomware são um tipo de ataque de malware em que os criminosos podem criptografar arquivos, exfiltrar (roubar) dados e ameaçar publicá-los, ou ambos, para coagir a vítima a pagar um resgate, geralmente em criptomoeda. Os invasores geralmente prometem fornecer chaves de descriptografia e/ou excluir os dados roubados assim que forem pagos. O ransomware tornou-se um meio de extorsão altamente popular por parte dos criminosos cibernéticos, à medida que modelos de trabalho remoto e híbrido expuseram os terminais a novas vulnerabilidades. Leia o artigo
Inteligência sobre ameaças é a coleta, análise e disseminação de informações sobre ameaças cibernéticas suspeitas, emergentes e ativas, incluindo vulnerabilidades, táticas, técnicas e procedimentos (TTPs) dos criminosos e indicadores de comprometimento (IOCs). As equipes de segurança a utilizam para identificar e mitigar riscos, reforçar os controles de segurança e guiar a resposta proativa a incidentes. Leia o artigo




