Turn the tables on advanced attackers inside your network
Attackers who gain access to your environment undetected think they've already won. Deploy deception technology for a proactive defense that lures and reveals sophisticated bad actors through realistic decoys.
Stop lateral movement
by cutting off attackers with convincing honeypots
Defend against GenAI attacks
on your infrastructure and learning datasets
Detect compromised users
and the abuse of stolen credentials
The Problem
Attackers compromise zero trust environments through users and apps
90%
80%
91%
Product Overview
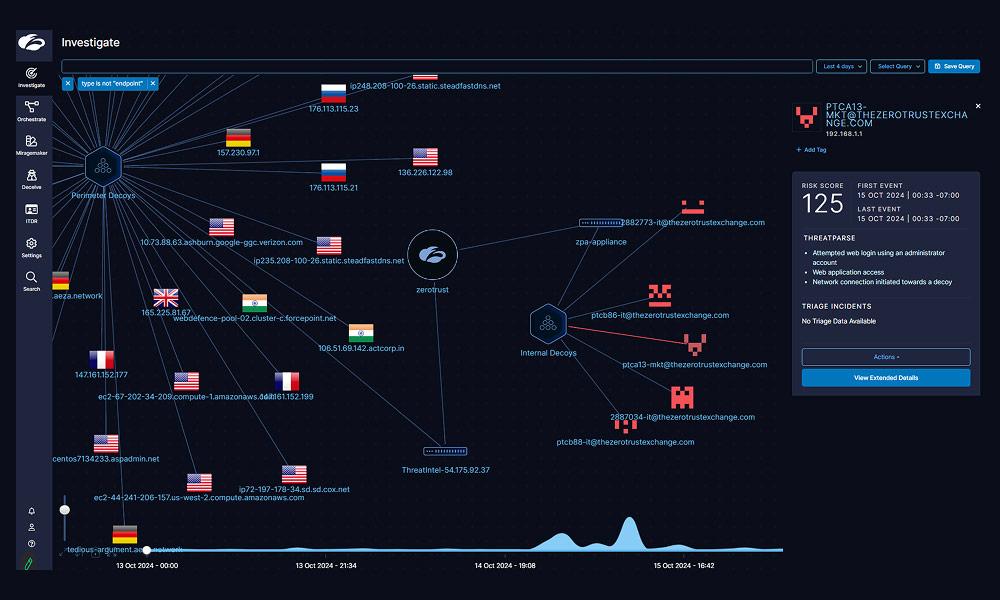
Detect advanced threats that evade traditional defenses
Zscaler Deception deploys realistic decoy assets across your environment to lure, detect, and intercept active attackers. When a compromised user interacts with a decoy, your team gets an immediate alert—attackers never know they've been caught until it's too late.
As part of the cloud native Zscaler Zero Trust Exchange™ platform, Deception can rapidly and seamlessly deploy high-fidelity threat detection throughout your enterprise.
De-risk your attack surface
Divert malicious actors away from critical targets like endpoints, identity systems, networks, applications, and the cloud.
Detect threats that matter, faster
Detect compromised users, lateral movement, and ransomware with high-confidence IOCs and near-zero false positives.
Contain threats in real time
Leverage zero trust access policies to dynamically limit or cut off access to sensitive SaaS services and internal applications.
Benefits
Take a fresh approach to targeted threat detection
Protect users and applications with decoys
Silently detect threats and attacker activity with endpoint lures as well as decoy applications, servers, users, and other resources.
Speed up incident response and reduce alert fatigue
Rapidly notify your security team of confirmed threats and breaches, with no false positives or added operational overhead.
Put the burden of success back on attackers
Replace your attack surface with convincing fake targets attackers can't resist, and catch them the moment they take the bait.
Product Details
A complete cyber deception platform
KEY CAPABILITIES
Use decoy chatbots, decoys LLM APIs, adaptive decoys, and decoy agents to detect attackers targeting GenAI infrastructure in your environment.
Use internet-facing decoys to detect pre-breach threats specifically targeting your organization.
Plant a minefield to protect your endpoints with decoy files, credentials, processes, and more.
Detect lateral movement in your cloud environments with decoy web and file servers, databases, and more.
Extract insights from context-rich logs, and get automated forensics and root cause analysis in two clicks.
Deploy decoy server systems that host services like SSH servers, databases, file shares, and more.
Detect enumeration activity and malicious access with fake users in Active Directory.
Gain deeper attack visibility in realistic, highly interactive decoy OS environments.
Use Cases
Make your network a hostile environment for attackers

Get early warning signals from perimeter decoys when advanced threat actors like ransomware operators or APT groups are performing pre-breach reconnaissance.

Deploy decoy passwords, cookies, sessions, bookmarks, and apps to detect compromised users when an attacker interacts with the deceptive environment.

Use application decoys and endpoint lures to divert and intercept attackers who are trying to move laterally in your environment.

Surround your high-value assets with decoys that detect and instantly block even the stealthiest and most sophisticated adversaries.

Detect ransomware at every stage of the attack life cycle with decoys in your network, endpoints, clouds, and Active Directory environments.

Integrate seamlessly with the Zscaler platform and third-party security operations tools like SIEM and SOAR to shut down active attackers with automated, rapid response.

Intercept attackers using stolen credentials to access decoy web apps that resemble vulnerable testbed applications and remote access services like VPNs.

Uncover prompt injection, data poisoning, and other severe attacks targeting your GenAI infrastructure and learning datasets.
The Zscaler Platform
The cybersecurity platform for the AI Age - built on Zero Trust to protect users, workloads, branches and devices through the world’s largest inline security cloud.

Data Security
Secure data everywhere, with comprehensive visibility and controls across all channels.
AI Security
Embrace AI with confidence using Zscaler AI Protect, a unified solution to secure AI at scale.
Agentic SecOps
Draw on insights from the world’s largest inline security cloud and third-party sources to assess risk and detect and contain breaches.
FAQ
FAQ
Zscaler Deception technology reimagines traditional honeypots by embedding deception directly into user environments across endpoints, network, Active Directory, cloud workloads, IoT/OT devices, and more, making traps indistinguishable from legitimate assets. Unlike static honeypots, Zscaler utilizes decoys and breadcrumbs, enabling attackers to unknowingly reveal themselves. This proactive, distributed strategy detects threats in real time and integrates seamlessly with the Zscaler Zero Trust Exchange platform.
Zscaler Deception is seamlessly woven into the Zscaler Zero Trust Exchange to dynamically distribute lightweight decoy assets across enterprise endpoints, networks, Active Directory, cloud workloads, and IoT/OT devices. These traps mirror authentic assets, making detection of malicious activity virtually instant. This embedded approach enables proactive threat detection while maintaining continuous validation for zero trust. Zscaler Deception is also built into the Zscaler Client Connector endpoint agent and Zscaler Private Access to detect lateral movement from endpoints to applications.
Zscaler Deception is designed to uncover a diverse range of threats, including advanced persistent threats (APTs), pre-breach attacks, identity compromise, privilege escalation, lateral movement, insider threats, and ransomware. By luring attackers with decoys and lures, it identifies suspicious behavior at early stages, providing proactive protection against breaches and reducing dwell times significantly.
Yes, Zscaler Deception fully supports cloud, on-premises, and hybrid environments. Its lightweight design ensures seamless deployment across endpoints, workloads, and IoT devices, regardless of the infrastructure. As a cloud-delivered solution, it aligns perfectly with modern distributed environments to provide comprehensive and scalable threat detection.
Yes, Zscaler Deception can detect attacks like prompt injection, data poisoning, jailbreaking, adversarial suffixes, training data extraction, and more. Zscaler Deception supports creating decoy LLM chatbots and APIs to detect these attacks.









