Providing security in a cloud-first world
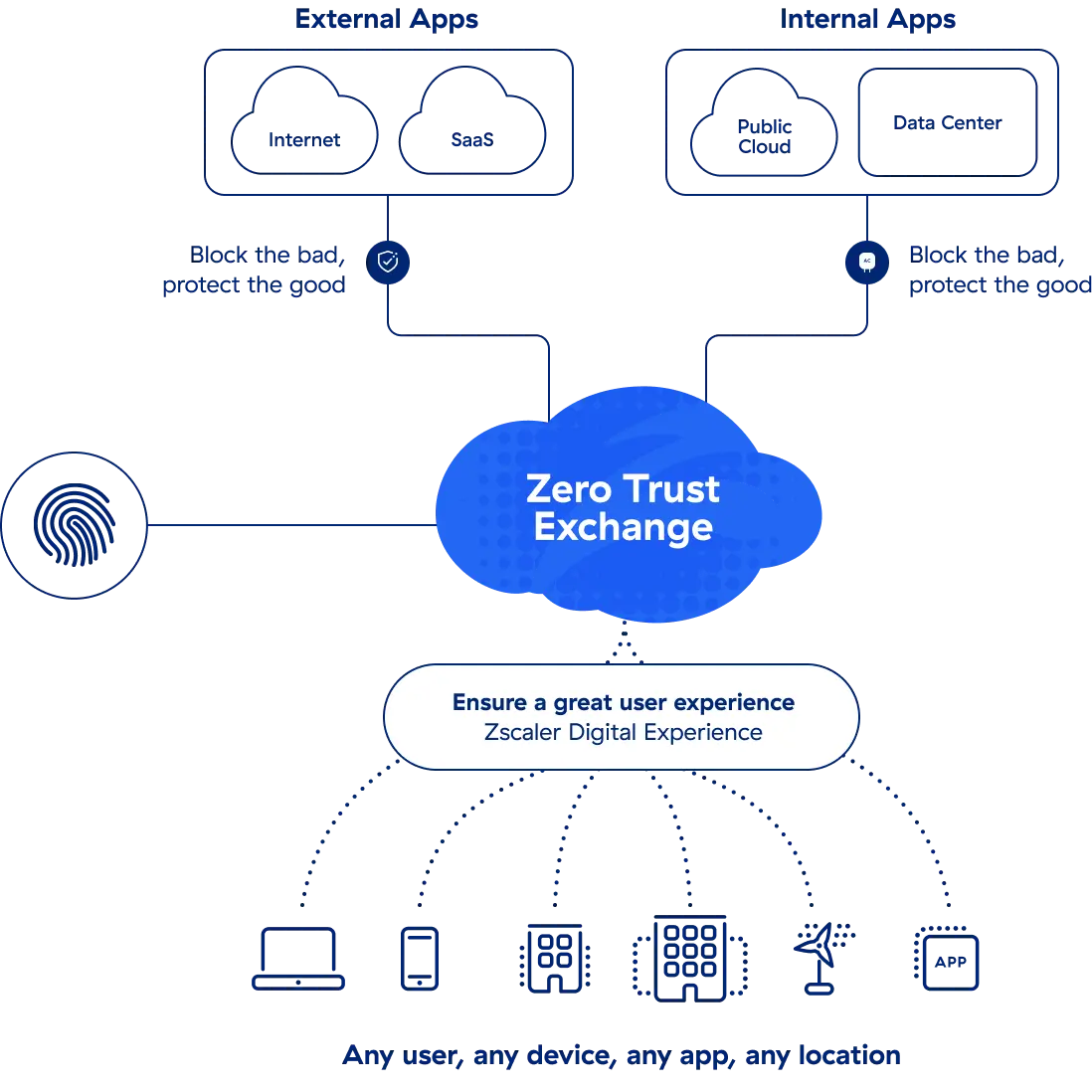
Organizations are adopting cloud-first strategies and zero trust security to support today’s work-from-anywhere environments. But as the network extends beyond traditional on-premises data centers and into the cloud, how do you protect employees wherever they work, regardless of the device or application they’re using? Current identity challenges include:
Poor user experiences
Increased risks
Complex processes
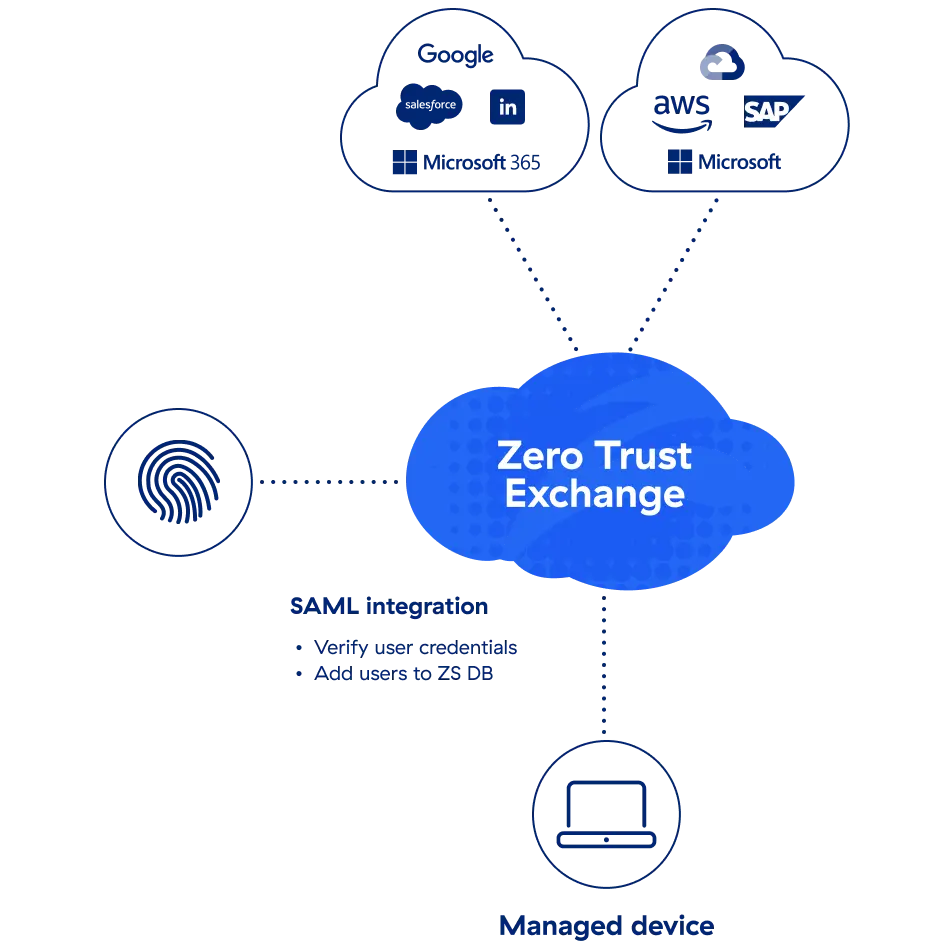
The first step to implement zero trust is to confirm the user is who they say they are. Once validated, access rights are verified based on context and the principles of least-privileged access to ensure users only have access to the applications for which they've been authorized. Zscaler integrates with leaders in identity and access management (IAM) as well as identity governance and administration (IGA).
The integrations between Zscaler and IAM partners deliver seamless authentication and improve the user experience.
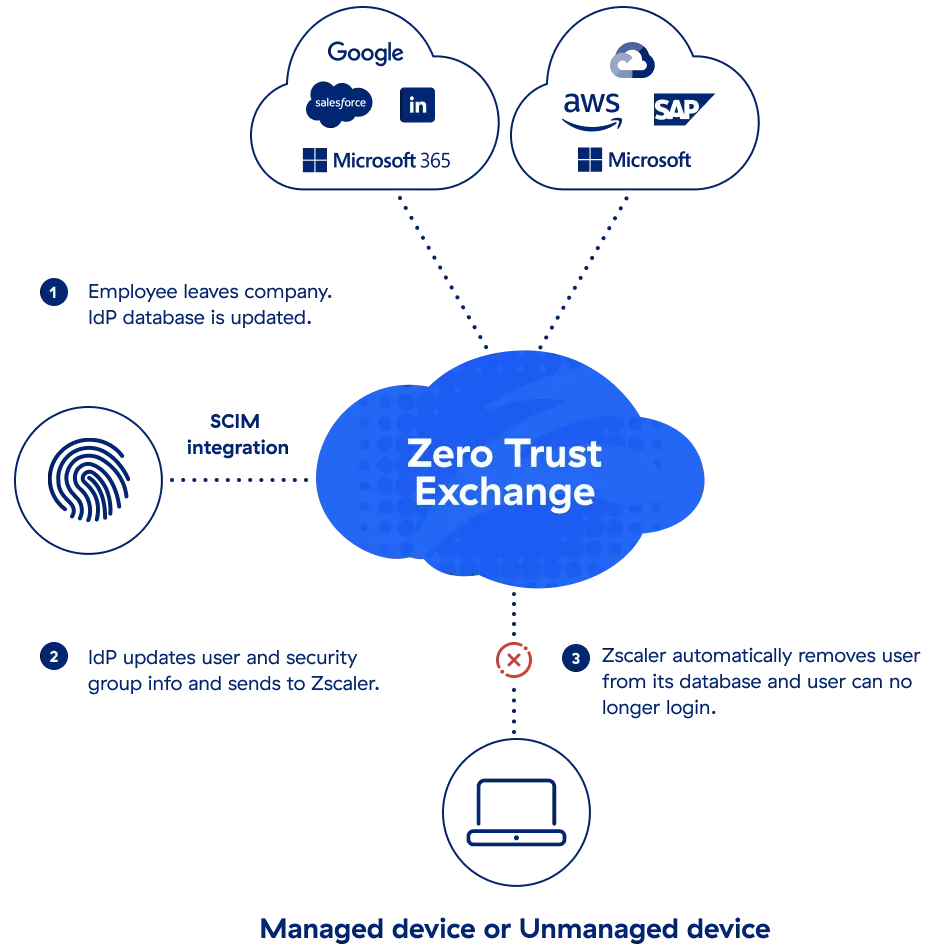
The integrations between Zscaler and IGA partners provide zero trust identity management, saving time, improving compliance, and reducing business risk