Blog da Zscaler
Receba as últimas atualizações do blog da Zscaler na sua caixa de entrada
Inscreva-se
Operation Endgame: Up In Smoke
Introduction
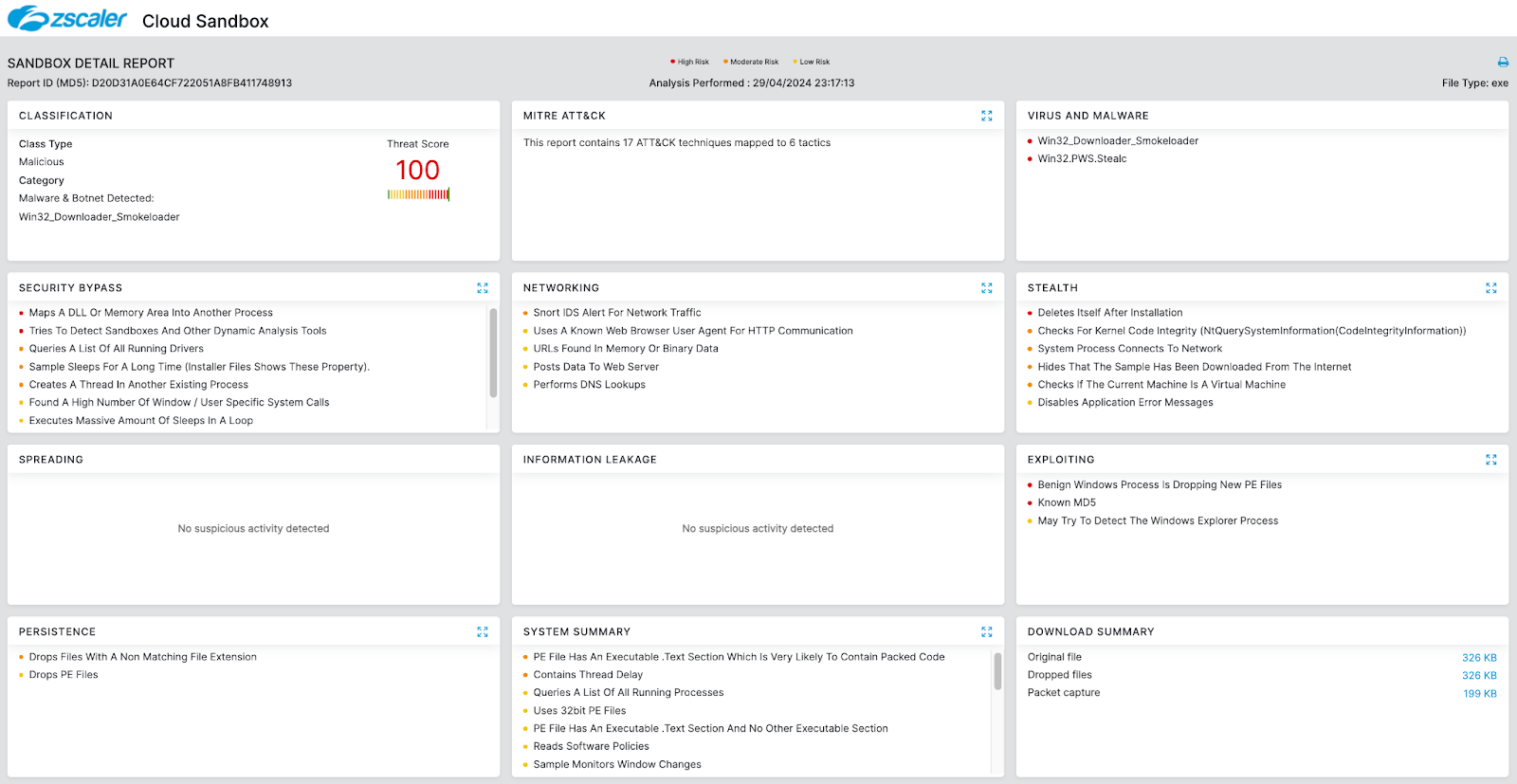
Smoke (a.k.a. SmokeLoader or Dofoil) is a malware loader that has been operational since 2011. Smoke is primarily used to deliver second-stage malware payloads including various trojans, ransomware, and information stealers. In addition, Smoke can deploy its own custom plugins that extend its functionality including mining cryptocurrency, harvesting credentials, and hijacking web browser data. Smoke is sold as a crimeware kit that enables a threat actor to easily set up and launch attacks. There are numerous versions of the kit that have had the server-side panel code leaked alongside cracked builders. This has led to a significant increase in the number of threat groups that leverage Smoke for malware distribution. Recently, Zscaler ThreatLabz has observed multiple malware families delivered through Smoke including Raspberry Robin, Stealc, and Stop ransomware.
In May 2024, Zscaler ThreatLabz’s technical analysis of Smoke malware supported an international law enforcement operation known as Endgame. This is the first major joint operation between law enforcement and private industry in Smoke’s existence.
In this blog, we analyze Smoke persistence mechanisms and communications, and examine how Operation Endgame dismantled its infrastructure and remotely cleaned up Smoke infections.
Key Takeaways
- In May 2024, Zscaler ThreatLabz’s technical analysis of Smoke assisted an international law enforcement operation known as Endgame to take over Smoke’s infrastructure and remotely uninstall the malware (when possible).
- Smoke is a malware downloader that originated in 2011 that is designed to deliver second stage malware payloads that include information stealers and ransomware.
- Smoke can deploy additional plugins that can be used to extend the malware’s functionality.
- Smoke has undergone extensive evolution over the years with numerous techniques to obfuscate its code and impede automated analysis.
- Despite being more than a decade old, Smoke typically receives updates every one to two years.
Technical Analysis
Numerous versions of Smoke have been released over the last decade. Our analysis will cover the last five versions of Smoke: 2017, 2018, 2019, 2020, and 2022. These version numbers roughly correspond to the year when the update was first observed. While Smoke uses a multi-stage loading process, our technical analysis will focus only on the main component of Smoke that performs the malicious functionality. There are three important parts that we will specifically analyze, which are relevant to Operation Endgame: installation, communication, and the uninstall command.
Installation
The installation process has slightly varied between Smoke versions. However, there are some commonalities that are shared across all versions. For example, Smoke generates a unique bot identifier that uses the same algorithm for all versions. Python code that replicates the bot ID generation algorithm is shown below:
import hashlib
bot_id = hashlib.md5(computername + hardcoded_constant + volume_serial).hexdigest().upper() + volume_serial.decode().upper()This bot ID value is used for a variety of purposes including the malware’s mutex name, executable filename, plugins’ filename, scheduled task name, etc. For example, Smoke version 2020 and 2022 use the code replicated below in Python to create the executable filename:
offset = 30
filename_len = 7
filename = ""
for i in range(filename_len):
filename += chr(ord(bot_id[i+offset]) - ord('0') + ord('a'))
print("executable filename:", filename)All versions of Smoke try to hide the executable file and plugins by setting the file attributes to SYSTEM and HIDDEN.
Table 1 below shows how the Smoke installation process has changed over time.
Smoke 2017 | Smoke 2018 | Smoke 2019 | Smoke 2020 | Smoke 2022 | |
|---|---|---|---|---|---|
Default installation location | %APPDATA%\Microsoft\Windows | %APPDATA%\Microsoft\Windows | %APPDATA% | %APPDATA% | %APPDATA% |
Creates an installation directory | Yes | Yes | No | No | No |
Executable filename length | 8 | 8 | 7 | 7 | 7 |
Scheduled task name | N/A | Opera scheduled Autoupdate %u | NvNgxUpdateCheckDaily_{%08X-%04X-%04X-%04X-%08X%04X} | Firefox Default Browser Agent %hs | Firefox Default Browser Agent %hs |
Other persistence mechanisms | Registry value / LNK shortcut in startup folder | LNK shortcut in startup folder | N/A | N/A | N/A |
Table 1: Comparison of Smoke installation techniques between versions.
Smoke versions 2017 and 2018 also create a directory to store the executable and plugins.
Network communication
All versions of Smoke since 2017 have a very similar network communication and packet structure. Network communications utilize HTTP POST requests to one or more hardcoded command-and-control (C2) servers. The HTTP POST body includes a packet structure that is encrypted using a hardcoded RC4 key.
The check in request (command 10001) contains the following information for Smoke versions 2020 and 2022 as shown in Figure 1:
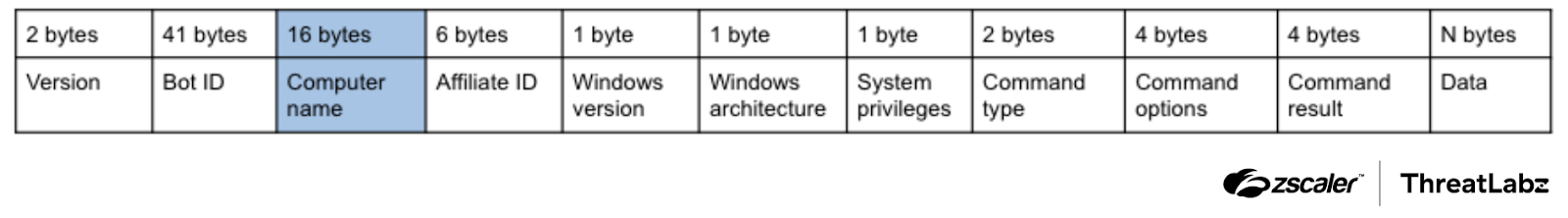
Figure 1: Smoke C2 request format (prior to encryption)
Versions 2017, 2018, and 2019 contain the same request format except the computer name field (highlighted in blue) is not present.
The first four bytes of the response are the size of the packet. The remaining response data is encrypted with a separate hardcoded RC4 key. The first two-byte value (when decrypted) is the Smoke version number (in little endian). The following bytes are then used to determine whether there are tasks or commands to execute. If the byte following the version number is 0x69, 0x72, or 0x75, Smoke interprets the value as one of the following commands:
Byte | Command | Description |
|---|---|---|
0x69 | i | Personal task |
0x72 | r | Uninstall |
0x75 | u | Update |
Table 2: Commands implemented by Smoke
Otherwise, the value is interpreted as the number of tasks to execute. The next section will provide insight into the operation of the uninstall command.
Remote cleanup
Smoke’s uninstall command performs the following actions:
- Terminates each Smoke plugin’s process
- Closes Smoke’s open handles
- Deletes the Smoke executable, plugins file, and scheduled task
- Erases and frees memory
- Terminates Smoke
In older versions of Smoke, including 2017 and 2018, there are artifacts left on the disk. In particular, the installation directory created by Smoke is not deleted, while Smoke version 2017 does not delete the registry value that was created for persistence. For newer versions, Windows specific forensic artifacts such as Amcache entries can be used to determine that a system was infected by Smoke. Furthermore, it is still possible to identify a system that was infected and cleaned up (via memory forensics), following the completion of the uninstall command. Note that the uninstall command does not free or unmap the section of memory allocated in explorer.exe that contains Smoke’s code.
Conclusion
Operation Endgame was the first major international law enforcement disruption of Smoke in over a decade. This will have an impact on the overall threat ecosystem, but will likely not be the end of Smoke. Zscaler will continue to work with industry partners, regional CERTs, and law enforcement agencies around the globe to protect our customers and ensure a more secure internet.
Zscaler Coverage
Zscaler’s multilayered cloud security platform detects indicators related to Smoke at various levels with the following threat names:
Indicators Of Compromise (IOCs)
Indicators | Description |
|---|---|
akmedia[.]in | Smoke C2 domain |
bethesdaserukam[.]org | Smoke C2 domain |
galandskiyher5[.]com | Smoke C2 domain |
gxutc2c[.]com | Smoke C2 domain |
host-file-host6[.]com | Smoke C2 domain |
host-host-file8[.]com | Smoke C2 domain |
humman[.]art | Smoke C2 domain |
kkudndkwatnfevcaqeefytqnh[.]top | Smoke C2 domain |
nidoe[.]org | Smoke C2 domain |
nuljjjnuli[.]org | Smoke C2 domain |
servermlogs27[.]xyz | Smoke C2 domain |
trad-einmyus[.]com | Smoke C2 domain |
trybobry[.]com[.]ua | Smoke C2 domain |
uohhunkmnfhbimtagizqgwpmv[.]to | Smoke C2 domain |
vacantion18ffeu[.]cc | Smoke C2 domain |
whxzqkbbtzvdyxdeseoiyujzs[.]co | Smoke C2 domain |
Esta postagem foi útil??
Receba as últimas atualizações do blog da Zscaler na sua caixa de entrada
Ao enviar o formulário, você concorda com nossa política de privacidade.



