Cero movimientos laterales. Cero superficies de ataque.
La segmentación Zero Trust sin agentes elimina el riesgo de movimiento lateral dentro de su fábrica aislando las líneas de producción y los puntos finales individuales sin añadir software.
Segmente fácilmente la TI de la OT y el IoT
Elimina los firewalls este-oeste y NAC
Implemente en horas sin tiempo de inactividad, agentes ni reajuste de VLAN
El problema
Arquitecturas heredadas, riesgos heredados
Los proyectos de segmentación manual de VLAN, NAC y ACL nunca finalizan.
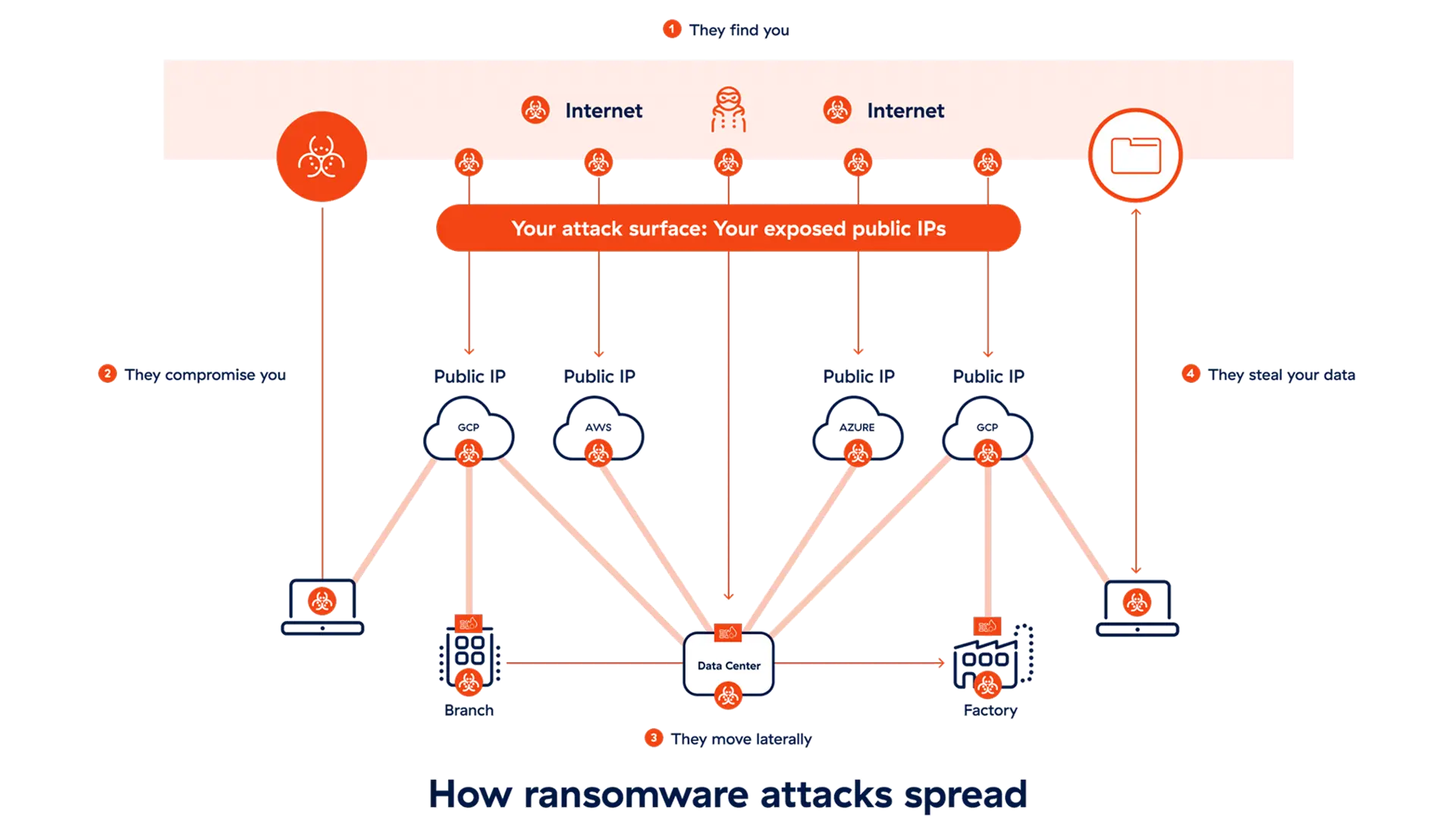
Infraestructura heredada combinada con sistemas modernos
Los dispositivos OT con décadas de antigüedad no pueden parchearse ni actualizarse, lo que deja vulnerabilidades críticas.
Más acceso de terceros
Los socios, los proveedores y la asistencia subcontratada exigen comunicaciones seguras y fluidas.
Redes planas y complejas
Las arquitecturas tradicionales facilitan la propagación de las amenazas una vez dentro.
Aumento de los ciberataques
Los sectores industriales, incluida la fabricación, fueron objeto del 22 % de los ataques de ransomware el año pasado.
Descripción general de las soluciones
La segmentación de OT/IoT de Zscaler es una solución sin agentes que sustituye a los firewalls, NAC y VLAN manuales. Aísle completamente sus dispositivos sin agentes, actualizaciones ni tiempo de inactividad. Mantenga seguras y operativas las máquinas heredadas y los sistemas sin supervisión. Con las políticas automatizadas, obtendrá una seguridad sencilla y que funciona a la perfección, sin ralentizar la producción.
Detalles de la solución
Mejore el tiempo de actividad y simplifique las operaciones
Eliminar errores de configuración manual. Capacite a los equipos locales de OT para gestionar los problemas rutinarios, aliviando la presión de los tickets de servicio para su equipo de asistencia técnica.

Capacidad
Aísle cada dispositivo en un segmento individual (usando /32).
Agrupe dispositivos, usuarios y aplicaciones para la aplicación de políticas automáticamente.
Aplique una política dinámica para el tráfico este-oeste e IT/OT, y separación de capas de Purdue.
Elimine los firewalls de este a oeste, los dispositivos NAC y el software basado en agentes.
Interruptor de seguridad contra ransomware
Automatice la respuesta a incidentes con una reducción de la superficie de ataque simple y seleccionable por el usuario. Simplemente elija un nivel de gravedad preestablecido para bloquear progresivamente los protocolos y puertos vulnerables conocidos.

Capacidad
Alinee la protección con el riesgo en tiempo real con cuatro niveles de política seleccionables según la gravedad.
Limite el acceso a las infraestructuras esenciales únicamente a direcciones MAC conocidas.
Integre perfectamente sus sistemas SIEM y SOAR existentes para obtener una respuesta automatizada.
Bloquee instantáneamente los protocolos más favorecidos por el ransomware, como RDP/SMB y SSH.
Comience por descubrir todos los dispositivos OT
Descubra y clasifique todos los activos del dispositivo en tiempo real, con total visibilidad y control de este a oeste. Recupere el control sin necesidad de implementar ni administrar agentes de puntos finales.

Capacidad
Detecte y clasifique automáticamente los dispositivos en el tráfico LAN este-oeste.
Establezca una base de datos de sus patrones de tráfico y comportamientos de dispositivos, e identifique el acceso autorizado y no autorizado.
Obtenga información precisa sobre la red para facilitar la gestión del rendimiento y el mapeo de amenazas.
Aproveche las integraciones de terceros para la realización de consultas y el etiquetado y la supervisión de alertas.
Ventajas
¿Qué diferencia a nuestra solución de segmentación de OT/IoT?
Sin agentes de terminal
Segmente completamente los servidores heredados, las máquinas sin supervisión y los dispositivos IoT/IoMT que no pueden aceptar agentes.
Una solución unificada
Implemente sin problemas la segmentación de OT/IoT integrada, la SD-WAN Zero Trust y el acceso remoto privilegiado (PRA).
Máximo tiempo de actividad
Implemente rápidamente y sin actualizaciones de hardware ni redireccionamiento de VLAN. Prolongue la vida útil de los equipos heredados.
Solicitar una demostración
Vea y asegure toda su segmentación crítica OT/IoT con la segmentación de dispositivos de Zero Trust. Permita que nuestros expertos le muestren cómo hacerlo.






