Blog Zscaler
Recevez les dernières mises à jour du blog de Zscaler dans votre boîte de réception
SASE vs. Zero Trust: What's the Difference?
Cybersecurity, like so many other areas of the tech world, is rife with jargon and acronyms. Knowing what each one means is part of the battle, but then comes understanding how they fit together—or don’t. In this blog post, we’ll unpack two related, but distinct terms: zero trust and SASE.
First off, industry hype is responsible for at least some of the confusion. Whenever a buzzworthy new tech term arises, countless vendors will race to attach it to their offering, even if the connection is tenuous at best.
Zero trust and SASE are among the most widely referenced terms in the cybersecurity world right now. Each of them is an architectural approach, and both of them drive stronger security and better experiences for organizations. So, what other attributes bring the two together, or else set them apart? To answer that question, let's first look at a quick comparison of these two architectures.
| Zero Trust Architecture | SASE Architecture | |
| Focus | Secures resources by continually verifying users, devices, and data access requests | Integrates networking and security to protect distributed users and cloud apps |
| Scope | Focuses on identity, access control, MFA, and device trust across hybrid environments | Integrates SD-WAN, SWG, ZTNA, CASB, and FWaaS into a unified cloud model |
| Use Case | Protects apps, systems, and data by preventing unauthorized access and lateral movement | Secures cloud native infrastructure, remote workers, and SaaS applications |
As you can see from the table, it's not precisely a question of "vs." between these architectures. Zero trust and SASE are more like two players on the same team, but with different positions. By definition, SASE relies on zero trust principles as part of its network transformation approach, forming an inseparable partnership.
With that said, let's examine these terms in more detail.
What is zero trust?
Zero trust is THE hot topic in cybersecurity, and every security vendor wants a piece of the action. Way back in 1994, Stephen Paul Marsh coined "zero trust" in his doctoral thesis, in which he referred to trust as something finite and definable, not subject to human interpretation. In other words, he asserted that we can objectively establish trust (or not) based on predetermined criteria.
A Forrester Research analyst first applied that logic to security and cloud applications in 2010. We should treat all network traffic as untrusted, he said, and allow no implicitly trusted users on the network. The technologies that used to protect us, and created trusted zones (typically behind VPNs and firewalls) simply don’t stand up to today’s advanced cybercriminals, armed with powerful tools to find and exploit vulnerabilities.
Zero trust can’t be built with VPNs and firewalls
Attention around the zero trust framework has grown, boosted by the steady migration of apps and services to the cloud, alongside the remote work boom that has defined the 2020s so far. On top of that, government mandates around the world have begun to specifically call out zero trust and drive its adoption.
If you’re new to zero trust, join one of our monthly introductory webinars. Our live experts will take you from key principles through practical use cases for rolling it out.
What is SASE?
Secure access service edge (SASE) has some overlap with zero trust, but it’s also a broader term. Analyst firm Gartner introduced the acronym (pronounced "sassy") in 2019. Like zero trust, SASE architecture requires some bold collaboration from security and networking teams to bring together software-defined wide area networking (SD-WAN) and multiple security technologies, including:
- Secure web gateway (SWG) to prevent unsecured internet traffic from entering the network
- Zero trust network access (ZTNA) to give users secure, least-privileged access to internal applications
- Cloud access security broker (CASB) to ensure secure, compliant use of cloud apps and services
- Firewall as a service (FWaaS) to deliver advanced threat prevention and access controls
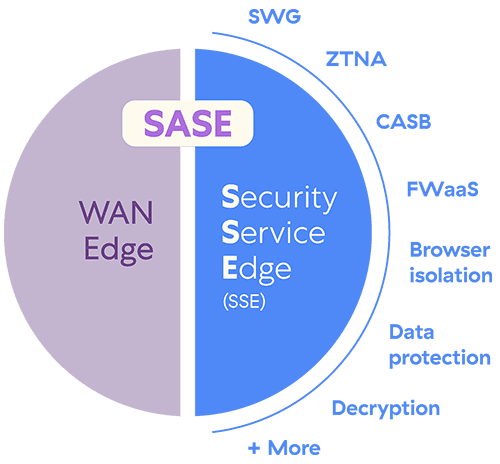
Interest in SASE has evolved. After an initial explosion, progress slowed as organizations realized the extent of change required to fully implement it. The COVID-19 pandemic added further drag because there was simply no need to redesign site connectivity for empty sites. So, organizations prioritized the security framework, without the networking, calling it security service edge (SSE).
Now that the return to work is well underway, SASE is working its way back into the spotlight. Still, it's a multifaceted solution that brings together a lot of different technologies. That's why many are looking to single-vendor solutions that eliminate the need to cobble together security and networking products from different suppliers.
At Zscaler, we take a different approach to SASE that removes the ineffective VPNs used by SD-WAN, preferred by traditional networking vendors for their SASE offerings. In place of VPN, Zscaler uses private encrypted tunnels to securely connect locations through our Zero Trust Exchange platform. We call it Zero Trust SD-WAN, an alternative approach that removes the risk of lateral threat movement inherent in traditional SD-WAN.
SASE overlaps with, but is distinct from zero trust
Implementing a SASE solution will partially deliver zero trust, but only for private applications. Zscaler offers the same zero trust approach for private applications, SaaS applications, internet access, and other application types. The zero trust principle "never trust, always verify" applies to all device, workload, user, and third-party traffic. Identity, user, and device context plus business policies are all considered before a connection is made to an application.
Learn more in this ESG research paper.
Which is better?
As you can see, zero trust and SASE are related in some ways. They differ insofar as you can roll out zero trust without SASE (as many have done with SSE), but you can’t build a robust SASE without zero trust elements. Sometimes, people ask us: which is better?
The ultimate goal is to protect everything, everywhere, making a zero trust framework foundational. By focusing on verifying every user, device, and action, zero trust creates a resilient security baseline. SASE then complements this by addressing cloud-first networking needs, like securing distributed teams and data flows.
While both are critical, adopting zero trust first ensures immediate protection against modern cyberthreats. With a strong security foundation in place, extending those principles into a SASE strategy ties together security and scalable networking to meet future demands.
Wherever you start, Zscaler has always been a pioneer in this space, and we’re ready to talk to you about how we can better protect your organization and its work.
Ready to explore how zero trust and SASE can revolutionize your security? Connect with one of our experts today.
FAQ
Which Is Better to Adopt First: Zero Trust or SASE?
Zero trust is the ideal first step, as it focuses on securing users, devices, and access to critical resources. Once that foundation is built, SASE extends zero trust principles to the cloud, combining security and networking into a unified platform with SD-WAN, CASB, FWaaS, and more.
Why Is Zero Trust Becoming So Popular?
Zero trust is gaining traction because it takes on modern threats with continuous verification of users, devices, and activity. With hybrid work, cloud expansion, and rising cyberattacks, it provides a scalable approach to reduce risks, protect SaaS apps, and meet strict compliance standards in today’s complex IT environments.
How Does Zscaler Align with Zero Trust and SASE?
Zscaler ties zero trust and SASE together, offering dynamic identity-based access, policy enforcement, and threat detection. Its unified platform secures users, cloud apps, and data through CASB, SWG, ZTNA, unified DLP, and more, delivering full protection for distributed users and hybrid infrastructures.
Cet article a-t-il été utile ?
Clause de non-responsabilité : Cet article de blog a été créé par Zscaler à des fins d’information uniquement et est fourni « en l’état » sans aucune garantie d’exactitude, d’exhaustivité ou de fiabilité. Zscaler n’assume aucune responsabilité pour toute erreur ou omission ou pour toute action prise sur la base des informations fournies. Tous les sites Web ou ressources de tiers liés à cet artcile de blog sont fournis pour des raisons de commodité uniquement, et Zscaler n’est pas responsable de leur contenu ni de leurs pratiques. Tout le contenu peut être modifié sans préavis. En accédant à ce blog, vous acceptez ces conditions et reconnaissez qu’il est de votre responsabilité de vérifier et d’utiliser les informations en fonction de vos besoins.
Recevez les dernières mises à jour du blog de Zscaler dans votre boîte de réception
En envoyant le formulaire, vous acceptez notre politique de confidentialité.




