Blog de Zscaler
Reciba en su bandeja de entrada las últimas actualizaciones del blog de Zscaler
Suscríbase
CVE Advisory: CVE-2024-3094 - Security Compromise in XZ Utils
Introduction
On March 29th, a security incident surfaced involving XZ Utils, a widely utilized data compression package integrated into major Linux distributions. Malicious code, allowing unauthorized remote SSH access, was discovered within versions 5.6.0 and 5.6.1 of XZ Utils. This exploit has been formally identified as CVE-2024-3094 and assigned a critical CVSS score of 10.
Background
XZ Utils fell victim to a sophisticated supply chain attack where attackers targeted the liblzma library, a crucial dependency utilized by OpenSSH. This attack allowed for the injection of code into an OpenSSH server, resulting in the potential for remote code execution (RCE).
The liblzma build process employs a series of intricate obfuscations to extract a prebuilt object file from a disguised test file within the source code. This object file is then utilized to modify specific functions within the liblzma library. Any software utilizing this modified version of the liblzma library is susceptible to data interception, modification, and breaches.
The malicious code was promptly discovered, and infected only the two most recent versions of the package, 5.6.0 and 5.6.1, both of which were released within the last month.
Affected Versions
The following table describes impacted distributions, along with a corresponding recommendation for each distribution.
| Distribution | Affected Systems | Affected Packages | Recommendation |
| Alpine Linux | Edge (active development) |
| Upgrade immediately to the latest version, 5.6.1-r2. |
| Arch Linux | N/A | 5.6.0-1, 5.6.1-1, and/or any release item that matches the following criteria:
| Upgrade immediately to the latest version, 5.6.1-2. |
| Debian | DebianUnstable (aka “Sid”) *This is a testing, unstable, & experimental version. | xz-utils 5.5.1alpha-0.1 (uploaded on 2024-02-01), up to and including 5.6.1-1. | Revert to 5.4.5 or upgrade to 5.6.1+really5.4.5-1. Note: No stable Debian versions are known to be impacted. Any compromised packages were part of Debian testing. |
| Kali | N/A | xz-utils 5.6.0-0.2 and/or any Kali installation updates made between March 26th and March 29th. | Apply the latest updates if you updated between March 26th and March 29th. |
| openSUSE |
| 5.6.0, and/or any updates that occurred between March 7th and March 28th. | Revert to 5.4.x. Note: For Tumbleweed users, you also have the option to upgrade to a new Tumbleweed snapshot (20240328 or later) containing the reversed version 5.6.1.revertto5.4 |
| Red Hat |
*Updated March 30, 2024: Fedora 40 beta does contain two affected versions of xz libraries - xz-libs-5.6.0-1.fc40.x86_64.rpm and xz-libs-5.6.0-2.fc40.x86_64.rpm. At this time, Fedora 40 does not appear to be affected by the actual malware exploit, but all Fedora 40 beta users are encouraged to revert to 5.4.x versions. |
| Revert to 5.4.x. Note: RedHat has advised users to immediately stop any instances of Fedora 41 or Fedora Rawhide, until XZ packages are reverted to safe versions. Red Hat Enterprise Linux (RHEL) was not impacted by this vulnerability. |
Table 1: A table listing impacted distributions, operating systems, and packages, along with recommendations to address the vulnerability.
Technical Details
The goal of the malicious backdoor implementing CVE-2024-3094 is to inject code into an OpenSSH server (SSHD) running on the victim's machine and allow remote attackers (who possess a certain private key) to send an arbitrary payload via SSH, which is executed before the authentication step and executes commands on the victim’s machine.
This supply chain attack uses multiple stages to decrypt obfuscated payloads and modify the build process of the XZ Utils tools. The obfuscated/encrypted stages and later binary backdoor are hidden in these two test files:
tests/files/bad-3-corrupt_lzma2.xztests/files/good-large_compressed.lzma
The figure below depicts the attack sequence an attacker could exploit.
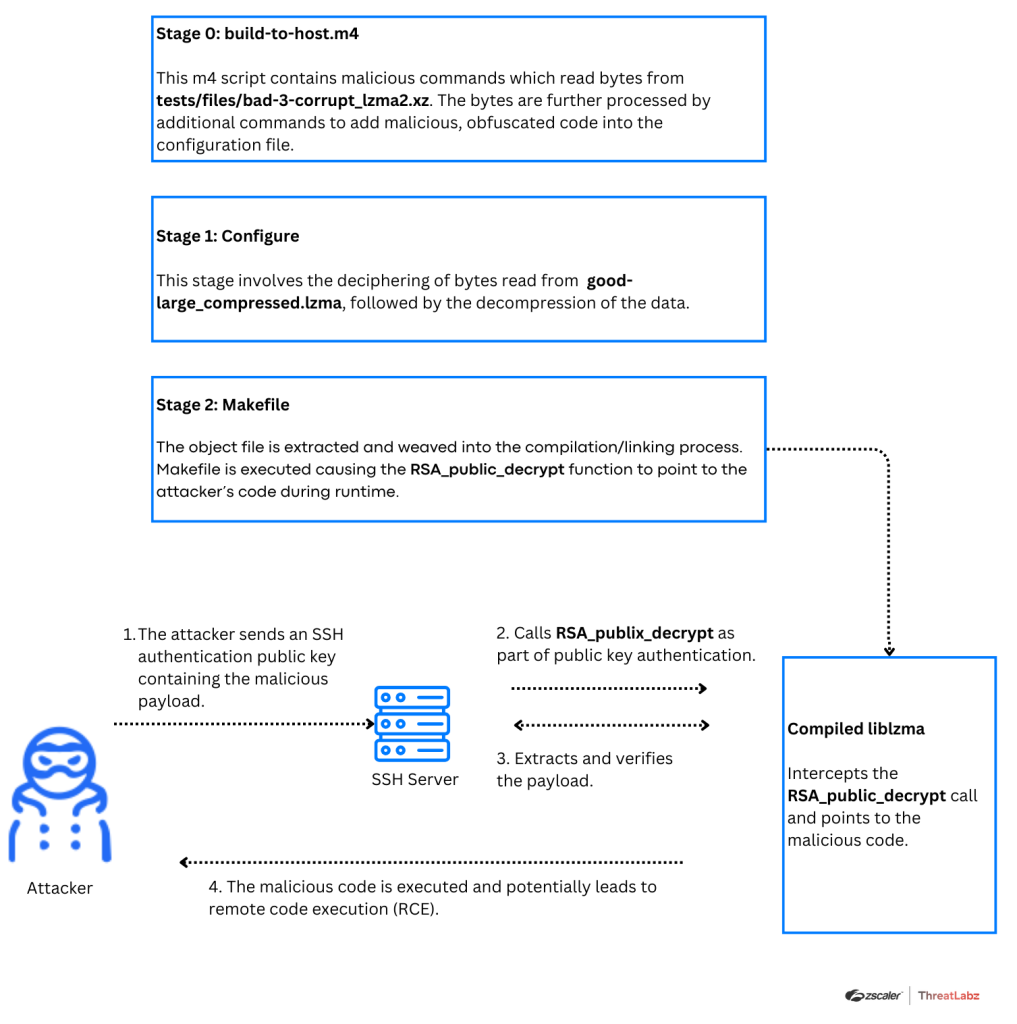
Figure 1: A diagram of the attack flow.
The build process uses the following command to ensure that the victim’s system is running on Linux and possesses a x86_64 architecture:
if ! (echo "$build" | grep -Eq "^x86_64" > /dev/null 2>&1) && (echo "$build" | grep -Eq "linux-gnu$" > /dev/null 2>&1); thenIn addition, the build process checks whether the .rpm package is Debian or Red Hat-based. It also inspects certain environmental variables such as TERM and LANG. The TERM variable is set after SSH client and server authentication. The malicious payload verifies that the TERM variable is not set and that the LANG variable is set, and ensures that the running binary is /usr/sbin/sshd as it won’t be relevant with other binaries.
After deciphering and decompressing the malicious payload over multiple stages, the payload is injected into liblzma.
The payload modifies the behavior of the RSA_public_decrypt function, which is used in verification of signatures. The payload decrypts the RSA public modulus N value from the attacker’s request and decrypts it using the ChaCha20 symmetric stream cipher. The validation of the decrypted data is done using the Ed448 elliptic curve signing algorithm.
Then, the decrypted payload is executed on the user’s SSH server. The backdoor contains only the public key, which ensures that only the attackers can generate valid payloads for the backdoor. The signature is bound to the host’s public key, meaning that a valid signature for one host cannot be reused for a different host.
Recommendations
In response to this threat, the Cybersecurity and Infrastructure Security Agency (CISA) has issued directives for affected individuals and organizations. XZ Utils developers and users are strongly advised to downgrade to a trusted, unaffected version of XZ Utils predating 5.6.0, such as 5.4.6 stable, or upgrade to a newer fixed version, if available.
Additionally, thorough audits of system logs and network traffic are encouraged to identify any signs of suspicious activity. Any findings should be promptly reported to CISA for further investigation.
How To Detect CVE-2024-3094
To check if your version of XZ Utils is impacted (5.6.0 or 5.6.1) run the following command:
$(which xz) --version | grep '5\.6\.[01]'
Zscaler Coverage
The Zscaler ThreatLabz team has deployed protection.
Zscaler Advanced Threat Protection:
Zscaler continues to monitor activities, through our telemetry data, potentially exploiting this vulnerability.
References
- https://jfrog.com/blog/xz-backdoor-attack-cve-2024-3094-all-you-need-to-know/#who-is-affected-by-cve-2024-3094
- https://www.redhat.com/en/blog/urgent-security-alert-fedora-41-and-rawhide-users
- https://vulcan.io/blog/alert-cve-2024-3094
- https://news.opensuse.org/2024/03/29/xz-backdoor/
- https://pkgs.alpinelinux.org/package/edge/main/x86/xz
- https://lists.debian.org/debian-security-announce/2024/msg00057.html
¿Este post ha sido útil?
Reciba en su bandeja de entrada las últimas actualizaciones del blog de Zscaler
Al enviar el formulario, acepta nuestra política de privacidad.



