Blog de Zscaler
Reciba en su bandeja de entrada las últimas actualizaciones del blog de Zscaler
Smarter and Faster Lateral Threat Mitigation with AI-powered App Segmentation
Zero trust prioritizes application protection over network segments, as networks are no longer central to application security(NIST publication). Exposed applications allow bad actors to move laterally, damaging business reputation. According to the Zscaler ThreatLabz 2024 VPN Risk Report, 32% of VPN attacks involved lateral movements, highlighting significant control challenges.
Application segmentation allows security teams to organize applications into discrete groups and provide least-privileged access, reducing the attack surface from internal access by authenticated users. Zscaler AI-powered App Segmentation enhances this by automatically generating recommendations for app segments and policies based on machine learning models, simplifying the implementation of app segments.
Zscaler AI-powered App Segmentation
ZPA is built based on the zero trust concept that all users/clients, including partners and other third-party users, must be authenticated, authorized, and continuously validated for security posture before being granted access through the Zscaler Zero Trust Exchange. Unlike a VPN, users do not connect to the network; they are only provided access to an allowed application per security policy. AI-powered App Segmentation, at the core of ZPA, plays an important role in this.

In the SSE framework, the software-defined perimeter ensures that only authorized users can access private applications via dedicated tunnels, eliminating the need for a traditional network perimeter. Zscaler AI-powered App Segmentation leverages AI/ML algorithms to:
- Identify and segment applications granularly
- Analyze transaction data to recommend user access
With its AI/ML engine, ZPA uses this data to enhance security policies, significantly reducing the attack surface. It dynamically adjusts access policies based on user requests, authentication, and device integrity, creating a secure tunnel directly to the specified application. This continuous monitoring and adaptive access make ZPA a leading solution for ZTNA-based private application access.
With ZPA, deploying user-to-app segmentation is straightforward and scalable. Simply define your application segments, implement policies, and then visualize the results of the segmentation.
- Bootstrapping Application Import from third-party sources, including but not limited to:
- Configuration management databases (CMDB) such as ServiceNow
- Vulnerability assessment providers such as Qualys and Tenable
- Cybersecurity asset management (CSAM) services
- App Discovery using wildcard app segments
- AI-powered recommendations to create app segments with user groups/departments based on transaction analysis
- Use actionable insights to further refine app segments and access policy by understanding user access
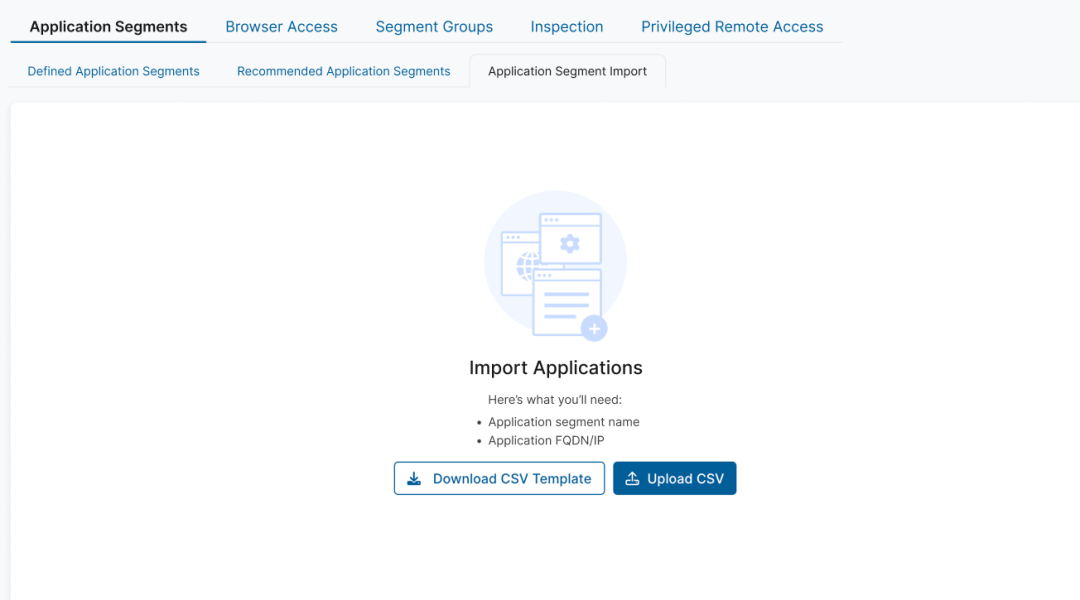
Import Applications
ZPA enables organizations to quickly onboard application information into ZPA and create application segments. Application segments consist of application details like FQDN, IP, TCP/UDP ports, etc.
Enterprises often maintain a system of record such as a CMDB or a CSAM, which is used to store infrastructure information like FQDNs, IPs, TCP/UDP ports, app owner details, location, importance of the application, and more. See an example of how you can ingest data from 3rd party applications here
The Application Segment Import capability enables you to import application segments to ZPA and start creating access policy rules, which become the starting point for your journey to zero trust.
App Discovery
App Discovery provides a powerful capability to dynamically discover the applications, which are not defined through the Import capability described above. Typically, most organizations don’t exactly know which applications are being onboarded and used in their environment, so they start with a “wildcard” app segment (e.g., *.private.acme.com with necessary ports open), which helps discover applications in use. Once a set of users has been onboarded, the discovery engine will be activated and report discovered applications on the dashboard with a 14-day cadence. This information can be downloaded for analysis, and administrators can create new app segments using selected applications from this list.

Intelligent Recommendations
Through the analysis of vast datasets, the AI/ML pipeline sequentially employs various segmentation techniques to generate precise, data-driven application segmentation outcomes. This include heuristic techniques; port/protocol-based, co-occurrence-based techniques; and state-of-the-art ML-based clustering techniques to generate app segments.
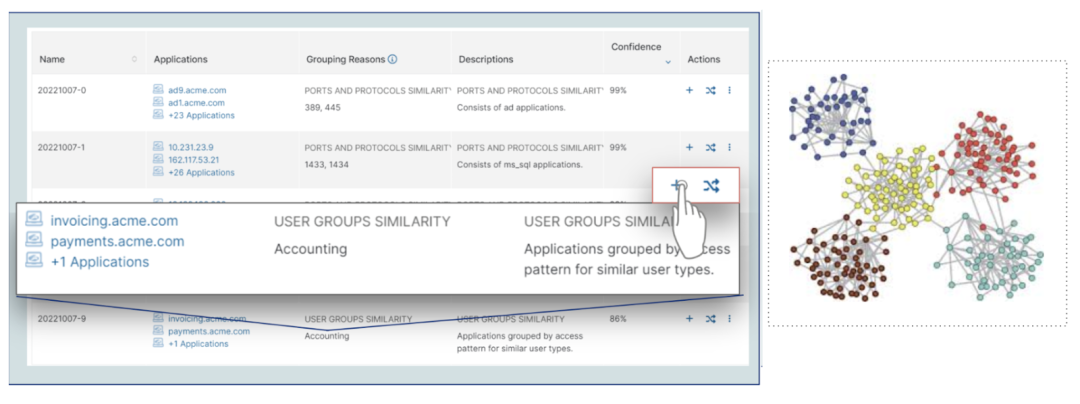
The app segment recommendations are derived from analysis of user access patterns, granularly choosing SCIM groups or departments for the given application. The ML algorithm works by selecting a minimal subset of SCIM groups that collectively cover all users seen accessing the applications in a segment while minimizing the number of users who have access. This subset forms the basis for defining access policies, ensuring comprehensive user coverage while minimizing the attack surface.
Each recommendation comes with a quantifiable attack surface reduction to enhance overall security posture. In the following example, if made part of an access policy rule, the recommendation would result in a nearly 90% attack surface reduction. This is achieved by the AI/ML algorithm studying user access behavior alongside application clustering to make the recommendation.
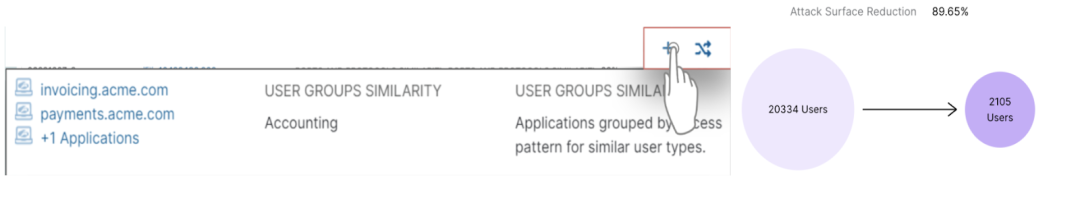
Adopting the recommended app segments and defining access policy will ultimately eliminate the need for wildcard app segments and help stop cyberthreats. Though this is an iterative process, it provides the most comprehensive and foolproof method of achieving user-to-app segmentation with proven results.
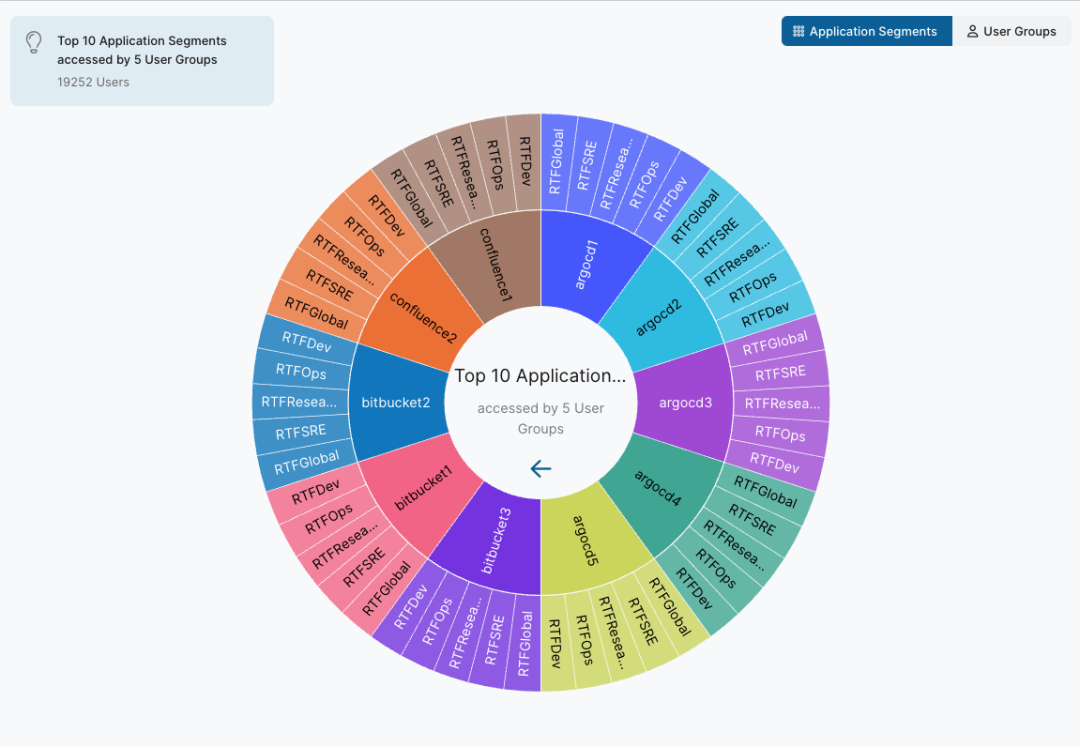
App Segmentation Insights
To define a granular access policy, you need to understand which users or user groups are accessing which applications. The App Segment Insights provides visibility into current app segments and users accessing them. These insights can be used to refine the segmentation continuously to implement least privilege access. The report supports user groups view and app segments view and lets you switch between them.
Administrators can view app segment/segment group to see the user groups that have accessed it or change the perspective to view the user groups to see which app segments/segment groups they have accessed.
From the detailed download option admins get in-depth information on which users, from which groups, are accessing which application segment or application (FQDN)
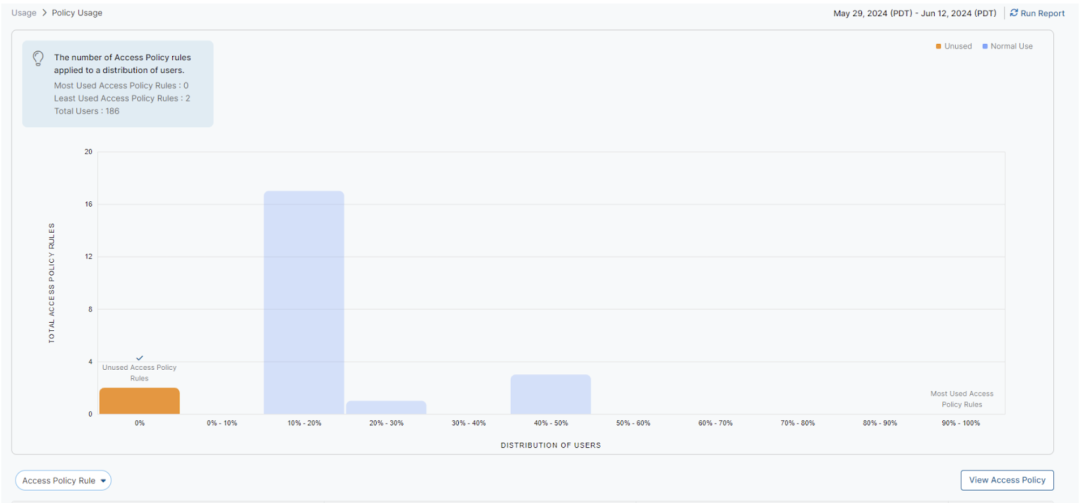
Policy Usage Insights
Understanding the usage of policy rules is essential to optimize the zero-trust journey. Policy Usage Insights offers a deeper understanding and details about the distribution of access policy rules used by users. These insights can help you assess overly permissive rules or determine unused access policy rules to potentially improve. Policy Usage Insights provides a view into:
- A percentage distribution of users by used access policy rules, for a high-level view of how policy rules are being used
- Most-used access policy rules, so application segments or access policies can be refined and made more granular
- Unused access policy rules, so they can be retired
Purchasing Segmentation Package as an Add-On License to ZPA
To accelerate your segmentation journey, actively utilize the features highlighted in this blog. All these features are accessible with the purchase of the Segmentation add-on license. Reach out to your Zscaler account team to gain a deeper understanding and activate features for your tenant.
The configurations necessary for these features can be found at the following ZPA help pages,Configuring Recommended Application Segmentation and Configuring Application Discovery, Application Import and Insights capabilities are automatically configured and ready to use upon enabling the Segmentation add-on license.
The ZPA team is working tirelessly to innovate and introduce exciting new capabilities in this area. Stay tuned for more updates in the future!
¿Este post ha sido útil?
Exención de responsabilidad: Este blog post ha sido creado por Zscaler con fines informativos exclusivamente y se ofrece "como es" sin ninguna garantía de precisión, integridad o fiabilidad. Zscaler no asume responsabilidad alguna por cualesquiera errores u omisiones ni por ninguna acción emprendida en base a la información suministrada. Cualesquiera sitios web de terceros o recursos vinculados a este blog se suministran exclusivamente por conveniencia y Zscaler no se hace responsable de su contenido o sus prácticas. Todo el contenido es susceptible a cambio sin previo aviso. Al acceder a este blog, usted acepta estas condiciones y reconoce su responsabilidad exclusiva de verificar y utilizar la información según sea precisa para sus necesidades.
Reciba en su bandeja de entrada las últimas actualizaciones del blog de Zscaler
Al enviar el formulario, acepta nuestra política de privacidad.



