Blog de Zscaler
Reciba en su bandeja de entrada las últimas actualizaciones del blog de Zscaler
Suscríbase
Real-Time Risk Mitigation with ZPA Adaptive Access Policy
In today's rapidly evolving security landscape, organizations must adapt quickly to security events. Alongside implementing secure private access using Zscaler Private Access (ZPA), monitoring user and device activity are crucial for enhancing security. Risky behaviors, such as clicking suspicious links or visiting malicious sites, can compromise devices and expose critical private data.
Traditional security measures using static access policy often fail to keep up with these threats, leaving gaps in protection. Adaptive Access Policy addresses this by offering dynamic, real-time protection.
ZPA Adaptive Access Policy can be configured to continuously assess a risky user's internet behavior or device posture changes and provide user-specific and device-specific enforcement based on these security events . The Policy takes effect for not only new sessions but also for existing sessions. This proactive approach ensures that critical private applications remain protected, even as threats and user actions evolve.
Key Benefits
- Real-time risk mitigation: By leveraging real-time signals from various user activity, ZPA Adaptive Access Policy dynamically adjusts user access, thereby reducing the window of opportunity for malicious actors.
- Enhanced security posture and operational efficiency: By integrating diverse signals into adaptive access decisions, it ensures a more robust security framework and minimizes the need for manual intervention, reducing administrative overhead and the potential for human error.
- Elevated user experience: By providing conditional access based on real-time evaluations, users are less likely to encounter unnecessary access denials, improving overall user experience.
Dynamic User Risk Scoring
Zscaler user risk scoring leverages previous behavior records to assign risk scores to individual users. This allows organizations to set dynamic access control policies based on various risk factors, accounting for the latest threat intelligence. Risk scoring empowers organizations to restrict access to sensitive applications for users with a high risk score until their risk profile improves. Zscaler Internet Access (ZIA) analyzes over 65 indicators and dynamically calculates a user’s risk score based on their internet activity.
The risk score has two components:
- Static (baseline) risk score: Review risky behavior for the past week and update every 24 hours
- Real-time risk score: Modifies baseline every 2 minutes and updates when the user comes in contact with malicious content (known or suspected)
The indicator of risky behaviors consist of the following:
- Pre-infection behavior: Malware blocked by ATP, Sandbox, malicious URL, etc.
- Post-infection behavior: Botnet traffic, Command & Control, etc.
- Suspicious behavior: Deny list, DLP violation, XSS, etc.
More information on how dynamic user risk scoring works, is available in a previous blog How Zscaler’s Dynamic User Risk Scoring Works
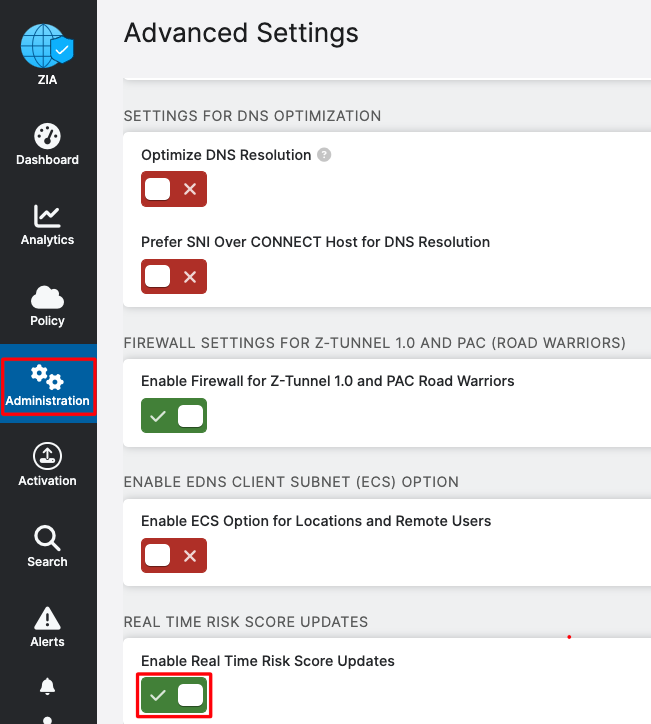
The dynamic user risk scoring needs to be enabled under Administration > Advanced Settings: Real Time Risk Score Updates:
ZIA administrators can view the user risk score under Administration > User Management:
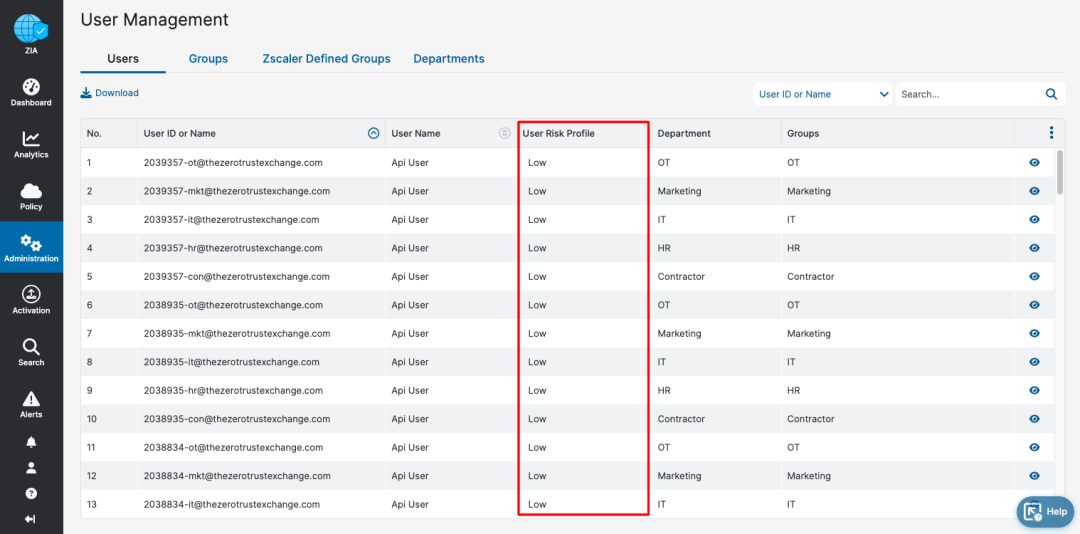
The dynamic user risk score generated by ZIA is shared with the associated ZPA tenant, allowing the configuration of the ZPA adaptive security policy.
Device Posture Check
The device posture check is configured in the Client Connector Mobile Portal under Administration > Device Posture: + Add Device Posture.
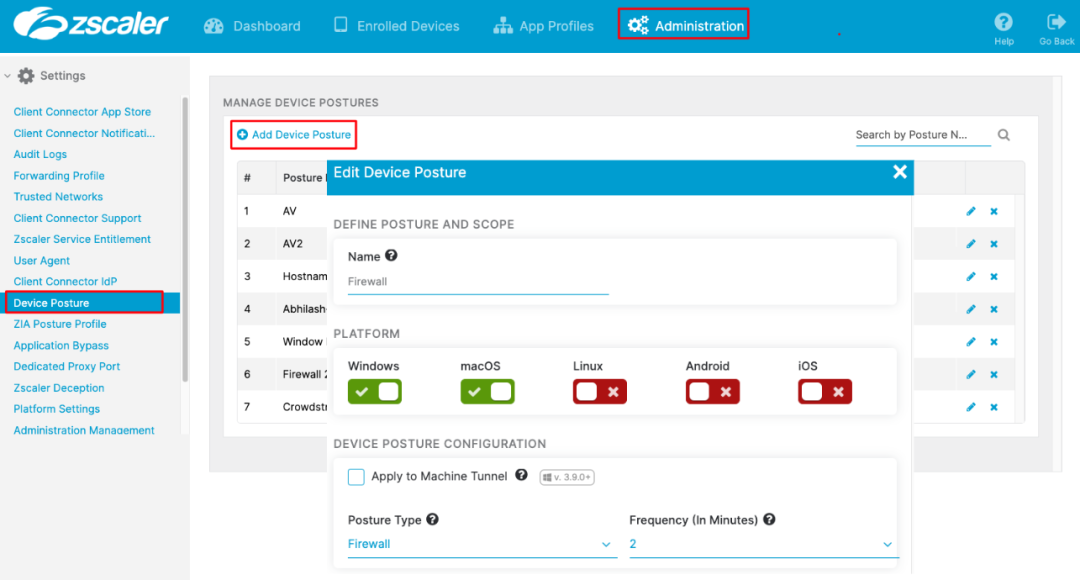
Note: The following posture checks are evaluated immediately when the posture changes, regardless of what is configured in the Frequency field:
- Process Check
- Detect Carbon Black
- Detect CrowdStrike
- Detect SentinelOne
- Detect Microsoft Defender
For more information on device posture check configuration, please refer to
https://help.zscaler.com/client-connector/configuring-device-posture-profiles
Adaptive Access Policy for Private Apps
ZPA access policy rule configuration supports multiple criteria. The most commonly used criteria are Application Segment or Segment Group and user SCIM or SAML attributes. Configuring User Risk Score and Device Posture checks in the access rule enforces the adaptive access policy.
The User Risk Score and Device Posture check are evaluated periodically. In case of user risk or device posture change, access to the application will be blocked, and existing active sessions for that specific user using the device will be terminated.
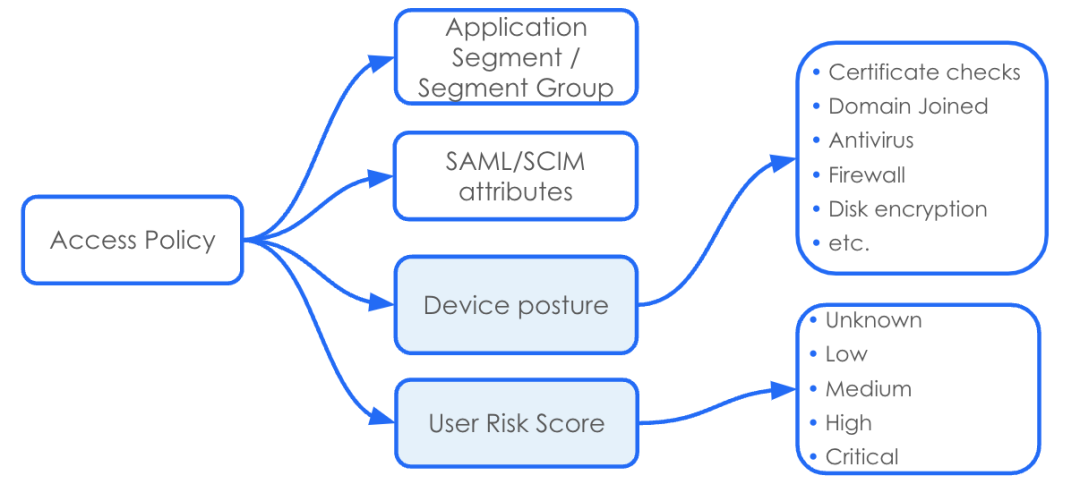
The screenshot below shows an example of an adaptive access policy rule. It allows access to the Linux server for the ZPAusers SCIM Group only when all device posture checks are met; and only when the user risk score is Low or Medium. All existing sessions will be terminated if the dynamic user risk score changes to High or Critical or if the device's posture fails.
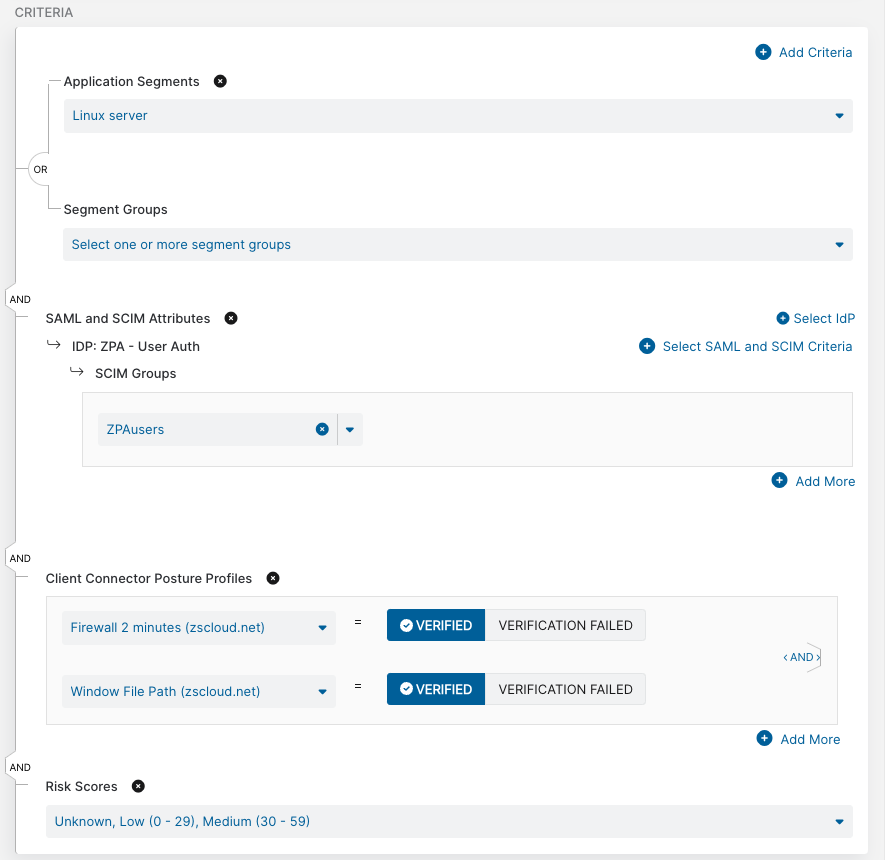
It is worth noting that this adaptive block access is applied to a single user or single device and is not a bulk action impacting all users. It is also possible to apply the adaptive security policy only to specific Application Segments or Segment Groups. This granular approach significantly reduces the risk of accidental denial of service.
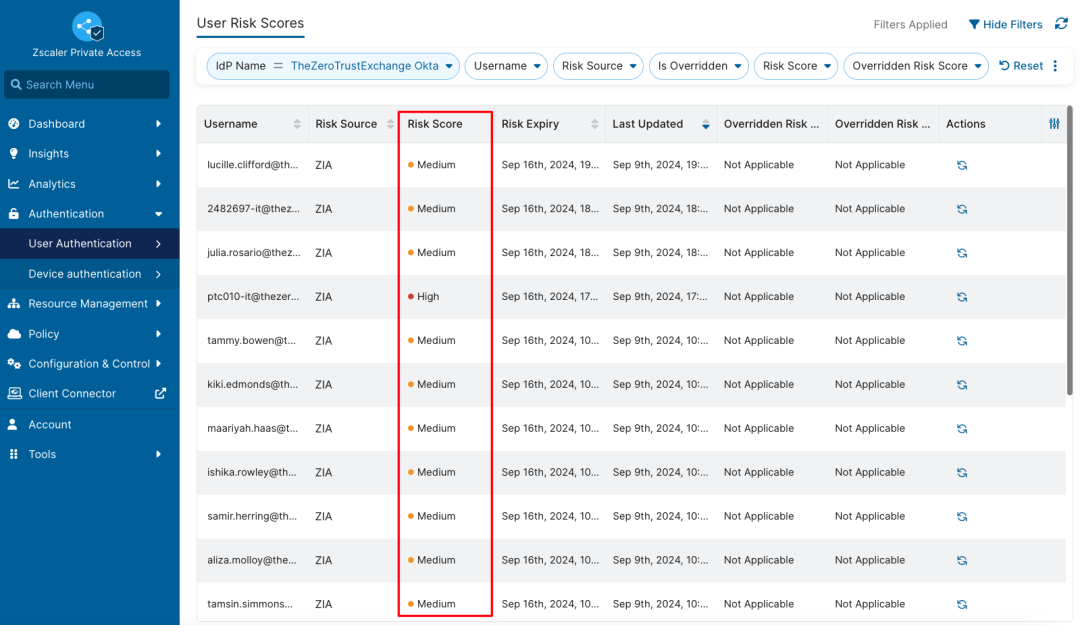
In the ZPA portal, the User Risk Score can be viewed under Authentication > User Authentication > User Risk Scores:
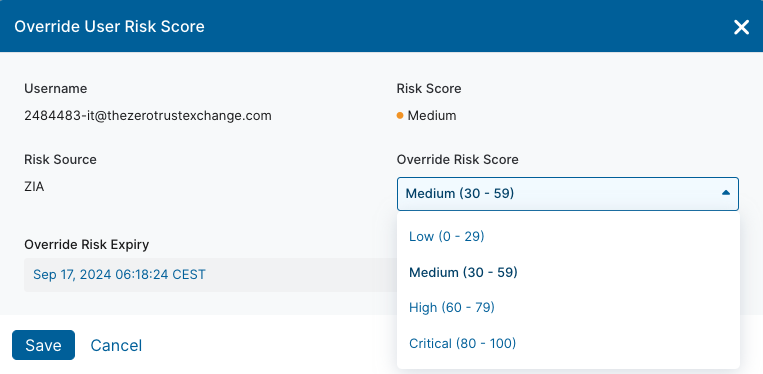
Furthermore, if needed, ZPA administrators can manually override the dynamic user risk score:
In summary, ZPA adaptive access policy continuously analyzes a user's internet access behavior and device posture. It performs automatic access blocks for individual users to private applications when the risk score is determined to be high. It provides the benefits of real-time risk mitigation, enhanced security posture, operational efficiency, elevated user experience, and support for a hybrid work environment.
If you're a ZPA customer, please reach out to your account team to enable adaptive access policy. To learn more about ZPA and how adaptive access can help you move to ZPA, click on our contact form.
¿Este post ha sido útil?
Reciba en su bandeja de entrada las últimas actualizaciones del blog de Zscaler
Al enviar el formulario, acepta nuestra política de privacidad.




