There is has been a recent surge in security blogs warning users to be extra cautious of a new spin on an old threat. Kelihos is a botnet which utilizes P2P communication to maintain its CnC Network. With all of the attention around Kelihos, it should be no surprise that 30/45 AV vendors are detecting the latest installer. I took some time to analyze recent threat reports that came through our malicious/suspicious files queue, to see if I could find anything to add. It didn't take long to find a now infamous iteration of this botnet installer in action. In particular, I found a file called "rasta01.exe".
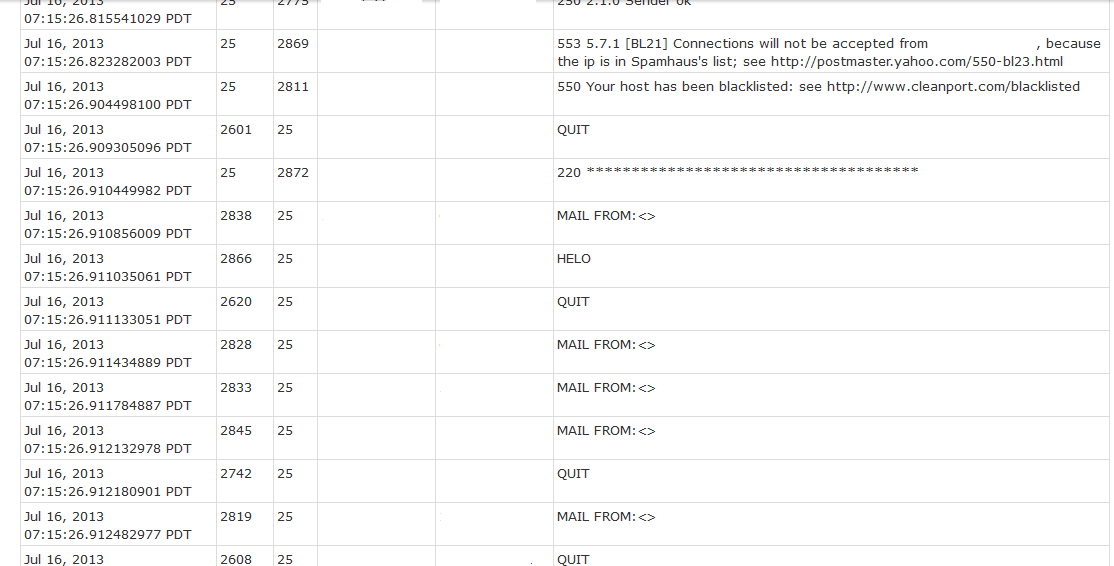
Besides the common naming convention of this threat, there are many other factors which gave this infection away at a glance. Firstly, the use of P2P style communication via SMTP raised an eyebrow. This particular instance called out to 159 distinct IP addresses.
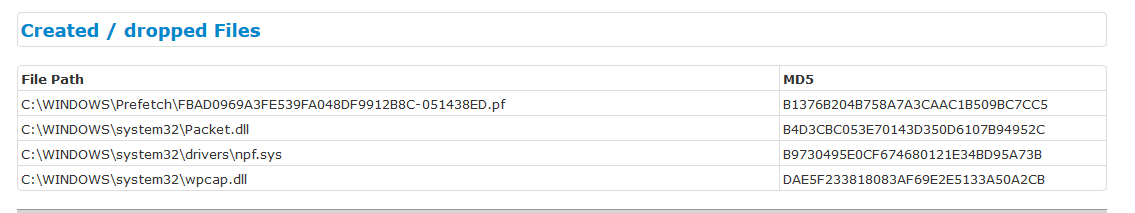 |
| Everything you need to monitor packets is created/dropped here. |
Next, I noticed that the botnet attempts to categorize it's new victim by using legitimate services to gather intelligence. In this instance, the malicious file actually queried the victim IP address on Barracuda Networks, SpamHaus, Mail-Abuse, and Sophos. These services primarily exist to notify users of abuse seen on the site or IP address. Kelihos is using it to to determine if the new victim is already seen as malicious or not. If the victim isn't seen in the CBLs (Composite Block Lists) yet, then it may be used as either a Proxy C&C or Spam-bot.
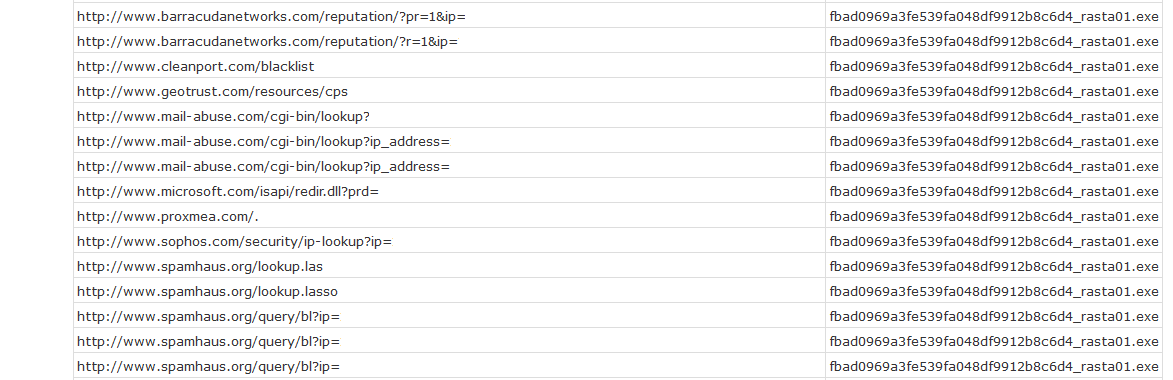 |
| References to CBL's from each location will determine what role the victim plays in the botnet. |