Critical Firewall and VPN Vulnerabilities Expose Your Business to Cyberattacks
It's time for a zero trust architecture.
Take advantage of Zscaler’s special offer
Concerned about recent firewall and VPN CVEs? Zscaler is offering a free attack surface assessment and professional consulting to help organizations move away from legacy architectures to zero trust.
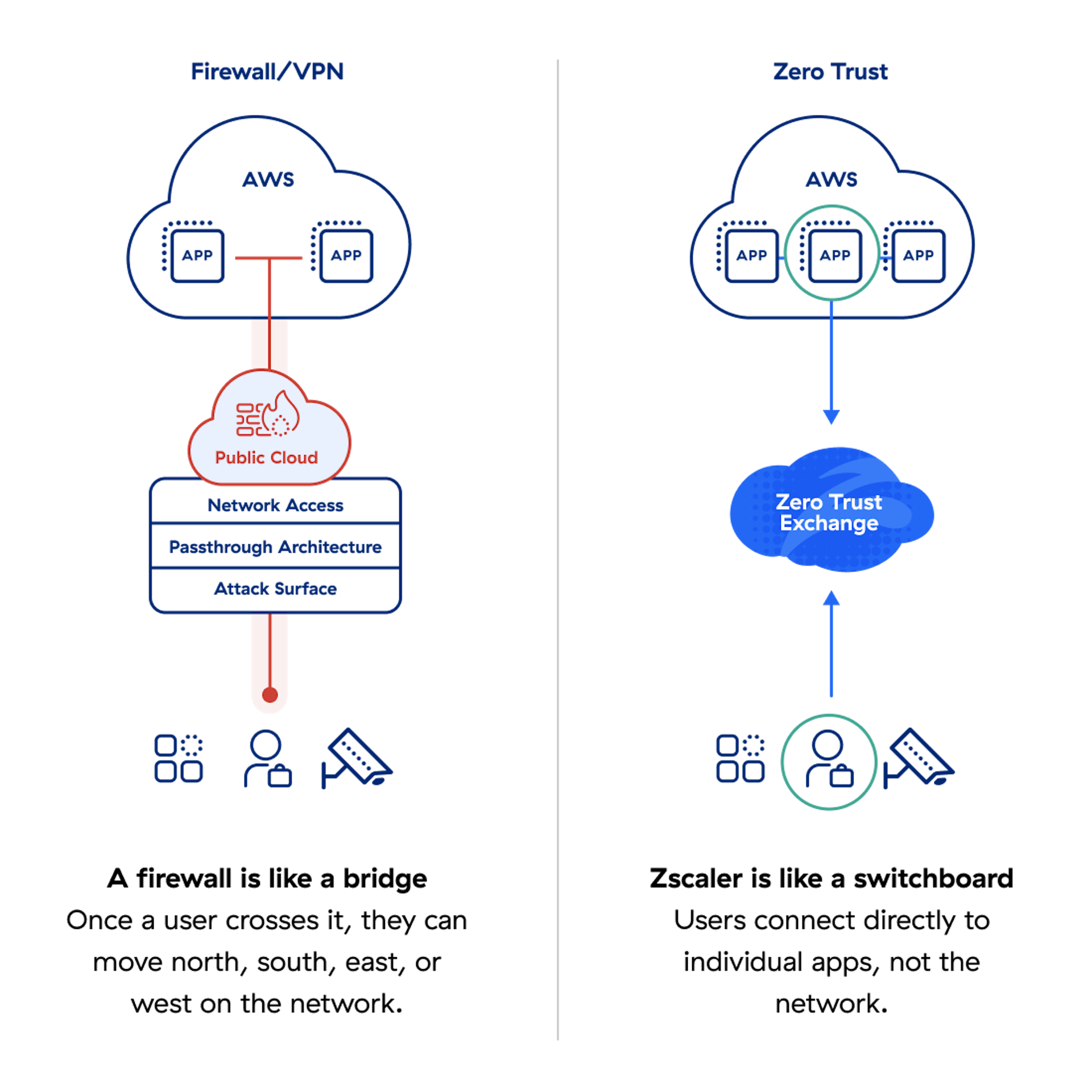
Firewalls and VPNs create vulnerabilities and fail to provide zero trust. Move away from legacy or cloud firewalls and VPNs to Zscaler.
- Avoid exposed devices or IP addresses. Keep users, branches, and factories hidden behind the Zscaler Zero Trust Exchange™ platform.
- Implement zero trust app access. Connect users directly to applications, not networks—and eliminate lateral threat movement.
- Get comprehensive attack surface management. See a holistic view of what’s exposed to the internet, vulnerabilities, and TLS/SSL weaknesses.
Built on the principle of least privilege, Zscaler’s cloud native, fully proxy-based architecture enables full TLS/SSL inspection at scale, with connections brokered between users and applications based on identity, context, and business policies.

Firewalls and VPNs expand your attack surface and leave you exposed.
In a year already marked by back-to-back disclosures of zero-day vulnerabilities from several leading vendors of firewalls and VPNs, the latest from Palo Alto Networks (CVE-2024-3400), with a CVSS score of 10, is a stark reminder that if you are reachable, you are breachable. These vulnerabilities act as a beachhead for attackers to launch sophisticated attacks and move laterally across flat networks.
Minimizes attack surface, prevents compromise, eliminates lateral movement, and stops data loss
Eliminates point products and complexity, which reduces business risk
Delivers AI-powered threat protection driven by 500 trillion daily signals and 400+ billion daily transactions
Provides actionable insights and guided workflows for remediation